Cross-border SaaS delivery in China operates under a partitioned model driven by regulatory sovereignty, data localization law, and geopolitical risk. Azure, Salesforce, Unity, and AI services have all bifurcated or been blocked. This analysis reconstructs the fragmentation pattern from the cited sources and delivers engineering lessons for teams operating across jurisdictions.
Introduction
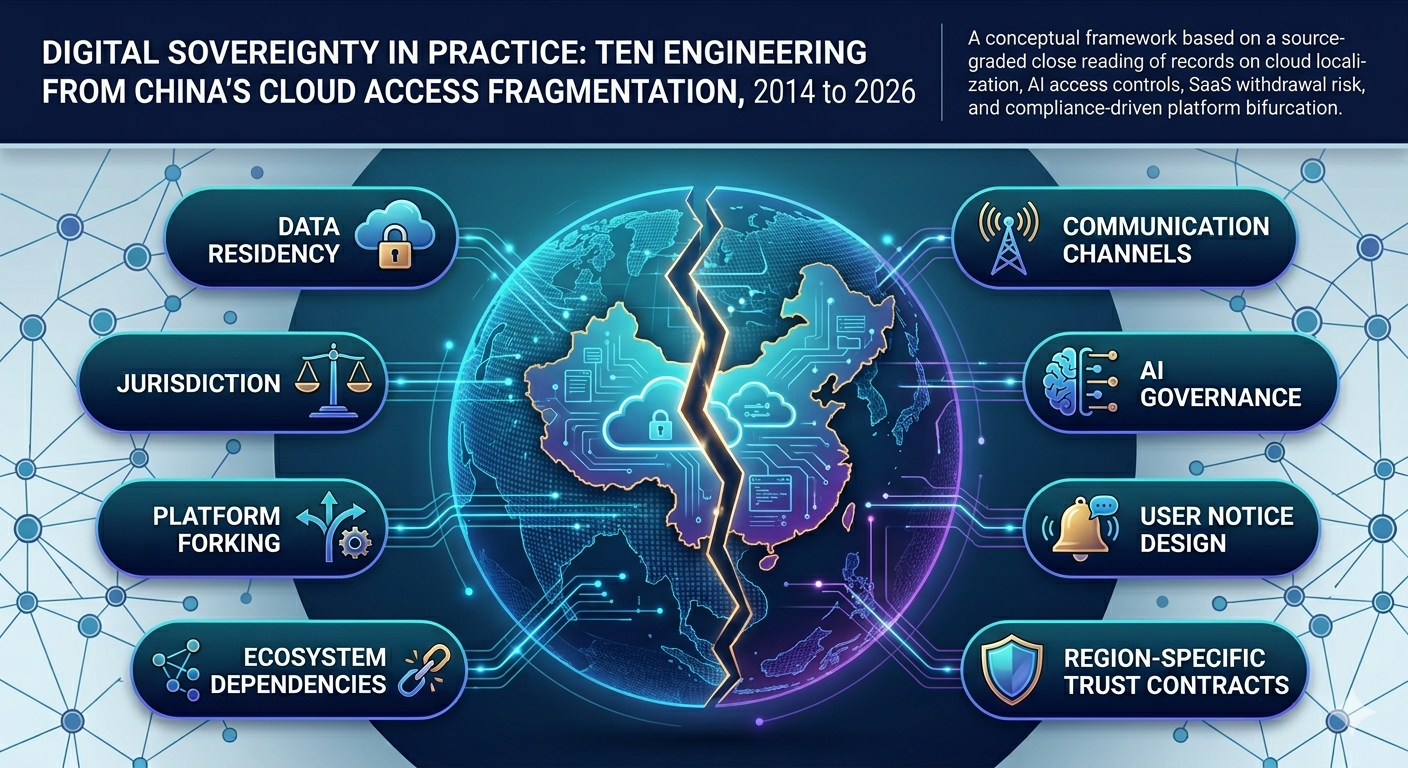
This article performs a close, source-graded reading of the cited records that span corporate announcements, vendor documentation, university operational advisories, industry media, and community incident discussions. A clear pattern emerges. Foreign platforms operating in China move from globally uniform delivery models toward localized control models shaped by legal jurisdiction, data governance constraints, and market-access design [1], [2], [7], [8]. Later records show this pattern extending into product-line divergence, region-specific service withdrawal, communication-channel asymmetry, and fragmented user access conditions [3], [4], [5], [6], [9], [12], [14], [15].
The analysis applies qualitative NLP techniques to the corpus, including sentiment profiling, semantic clustering, and constrained counterfactual framing. The practical output is a ten-lesson framework for engineering, security, legal compliance, platform operations, and governance teams. Each lesson incorporates explainability, interpretability, and trustworthiness as embedded operational criteria, not as detached theory.
Jurisdiction and Interpretation Boundary
This article evaluates operating-model evidence and user-impact reports across multiple source tiers. It does not infer political intent from a single event and does not treat community posts as standalone proof. Where records conflict or remain incomplete, the analysis preserves uncertainty and flags the gap. This article is not legal advice.
Quick Definitions
- Digital sovereignty
- The capacity of a state or jurisdiction to exercise legal and operational control over digital infrastructure, data flows, and platform access within its borders.
- Platform bifurcation
- The splitting of a global software platform into region-specific versions with divergent features, data handling, and operational governance.
- Data localisation
- A regulatory requirement that certain categories of data must be stored, processed, or managed within a defined geographic jurisdiction.
- Cloud access fragmentation
- The condition in which users in different jurisdictions experience unequal service availability, feature sets, or escalation pathways from the same cloud provider.
- Sovereign-aware architecture
- A system design that treats legal jurisdiction, data residency, and operator accountability as first-class architectural dimensions rather than deployment-time exceptions.
Why This Matters
Cross-border cloud planning for China now requires jurisdiction-aware architecture by default. Earlier assumptions treated global SaaS as one coherent operating surface. The current record shows a segmented reality where service availability, feature parity, escalation pathways, and data handling behavior can diverge by billing region, control ownership, and legal exposure [1], [2], [6], [10], [11], [14].
This study treats the provided links as a unified corpus. The method stays conservative. It separates documented facts from plausible inference and then maps the result to practical controls.
Evidence Base and Method
The corpus contains sources with uneven evidentiary strength. Official and institutional records provide the strongest anchors for dates, policy text, and operating conditions [1], [2], [5], [6], [14]. Industry media contributes useful comparative interpretation with mixed depth [3], [4], [7], [8], [10], [13]. Community discussions provide high-sensitivity incident signals but weaker formal verification [9], [15]. One source openly states AI-assisted drafting, so the text requires stricter provenance control during reuse [12].
The NLP workflow used three passes. The first pass extracted timeline markers and named entities to validate chronological coherence. The second pass grouped semantically related terms around localization, compliance, restriction, migration, suspension, and deletion. The third pass applied constrained counterfactual prompts to identify avoidable governance failures under alternate execution choices. This approach does not create new facts. It exposes structural relationships inside the supplied material.
Close Reading and Timeline Reconstruction
In March 2014, Microsoft announced general availability of Azure in China through 21Vianet operations and framed the model around local compliance and data independence [2]. This early milestone set a durable pattern. Entry required local operating structure rather than direct global continuity.
In July 2019, Salesforce and Alibaba established Alibaba Cloud as the exclusive provider route for Salesforce CRM in mainland China, Hong Kong, Macau, and Taiwan [1], [7], [8]. Public messaging emphasized customer enablement, yet the operational implication was broader. Control boundaries shifted from direct global service delivery to region-scoped channel governance.
Follow-on reporting within the same partnership cycle moved from announcement language toward operational implications such as migration and privacy-compliance posture [1], [7], [8]. The transition from market-entry framing to delivery-model interpretation became explicit.
From 2025 to 2026, this fragmentation accelerated in developer tooling. Unity coverage reported withdrawal of Unity 6 access in mainland China, Hong Kong, and Macau, paired with a localized engine path for that market [3], [13]. Siliconera reported Asset Store separation and purchase constraints after the regional cutoff [4]. The technical implication is direct. Ecosystem continuity may fail before core runtime continuity fails.
Service asymmetry appears outside game tooling as well. Cornell IT documented Adobe Acrobat Sign restrictions for mainland China IPs from 30 June 2025, while explicitly excluding Hong Kong from that specific change notice [14]. Operational guidance then moved to handwritten signature contingency pathways.
Atlassian documentation for Opsgenie showed country-tiered SMS and voice support and included a China-specific warning on telecom-level SMS delivery blocking [6]. The design inference is precise. Alert-channel assumptions cannot remain globally uniform.
Canvas support guidance from Florida State University described intermittent access, throttling, and blocked dependencies for tools embedded in learning workflows [5]. Because this source comes from institutional operations, it provides practical visibility into user-level friction.
AI access controls introduced a sharper policy boundary in 2024 and 2025 reporting. RFA reported OpenAI traffic blocking for China, Hong Kong, and Macau in July 2024 [11]. CRN Asia reported Anthropic policy expansion toward ownership-structure screening beyond location checks [10]. Combined reading suggests that governance logic now couples jurisdiction with control-structure analysis.
Community sources contribute early detection value but require strict caution. A Reddit GitLab thread reports user-received migration and servicing notices linked to JiHu pathways, yet comments contain contradiction and disputed interpretation [9]. A GitHub community discussion captures broad user reports of temporary access restriction and later maintainer resolution signaling, though much of the thread remains anecdotal [15]. These sources provide incident signal, not standalone policy proof.
The linked yage.ai article offers a detailed synthesis of Slack workspace events and clearly marks uncertainty boundaries, yet the page also discloses AI-assisted authorship [12]. Analytical reuse stays valid only when each claim remains tied to verifiable primary sources.
NLP Findings Across the Corpus
Sentiment profiling by source type shows a stable polarity divide. Corporate and institutional pages use reassurance language around enablement, support, compliance, and continuity [1], [2], [6], [14]. Community and disruption narratives use loss language around blocked access, suspension, restriction, and deletion [9], [12], [15]. This contrast does not prove deception. It reflects role-driven communication priorities.
Embedding-style thematic grouping yields four dense clusters. The first cluster links compliance, localization, data residency, and regulatory alignment [1], [2], [7], [8], [14]. The second cluster links product splitting, localized engines, regional distribution, and asset ecosystem divergence [3], [4], [13]. The third cluster links access block events, suspension pathways, migration pressure, and deletion windows [9], [10], [11], [12], [15]. The fourth cluster links communication channels, telecom constraints, and continuity risk [5], [6], [14].
Counterfactual framing highlights one repeated governance lever. Exit programs with weak notification architecture produce high-friction user outcomes even when a legal rationale exists. Multi-channel notice, staged export rights, and documented migration tooling reduce avoidable trust erosion. This framing does not alter factual claims. It identifies preventable execution failure.
Critical Evaluation of Source Strength and Limits
Official and institutional pages provide the strongest factual substrate for dates, policy wording, and operating constraints [1], [2], [5], [6], [14]. Trade media adds meaningful market context and comparative interpretation, though access barriers can limit transparent quote extraction in some cases [3], [4], [7], [8], [10], [13].
Community discussions are valuable for rapid detection of user-impact surfaces and practical artifacts such as quoted notices and screenshots [9], [15]. Verification remains uneven because first-hand observation, speculation, sarcasm, and secondary reporting often coexist in one thread. These sources remain analytically useful when handled as provisional inputs and then triangulated.
The linked yage.ai draft offers coherent synthesis scaffolding and explicit uncertainty notation [12]. AI-assisted composition, however, can produce fluent overreach if claims are not checked line by line. This analysis therefore treats that source as an interpretive aid rather than a primary factual anchor.
Ten Lessons for Engineering, Security, and Governance
1. Architectures Need Jurisdiction as a First-Class Dimension
Global-default cloud design fails when legal domains impose divergent control requirements. Azure through 21Vianet and Salesforce through Alibaba show that regional entry can require structural operating redesign [1], [2], [7], [8]. Explainability improves when architecture artifacts make legal boundary, data boundary, and operator boundary explicit.
Actionable recommendation: define jurisdiction-aware reference architectures with mandatory controls for data placement, key custody path, and operator responsibility matrix before workload onboarding begins.
2. Partnership Models Shift Accountability Maps
Localization partnerships can preserve market access while fragmenting accountability for availability, incident response, and compliance attestation [1], [7], [8]. Interpretability depends on clear control mapping across legal entity, infrastructure operator, and customer-facing support responsibility.
Actionable recommendation: maintain a living responsibility crosswalk that aligns contractual clauses, technical controls, and escalation paths for every partner-operated region.
3. Data Residency Must Be Engineered, Not Declared
The corpus repeatedly links service viability to data localization and transfer-control obligations [2], [7], [8], [14]. Trustworthiness increases when data lineage, replication policy, and egress authorization remain auditable across regions.
Actionable recommendation: implement policy-driven data routing with immutable lineage logs and periodic legal-control reconciliation against jurisdiction-specific obligations.
4. Product-Line Forking Requires Release Governance Discipline
Unity records show region-specific engine divergence and ecosystem partitioning between global and China-specific channels [3], [4], [13]. Explainability for downstream teams requires explicit disclosure of parity gaps, deprecations, and compatibility limits.
Actionable recommendation: run dual release trains with a formal divergence register and regression tests that detect behavior drift between region branches.
5. Ecosystem Dependencies Can Fail Before Core Platform Access Fails
Asset-store restrictions show that ecosystem dependencies may fail earlier than core engine access [4]. Interpretability improves when dependency inventories include legal availability tags, support lifecycle windows, and region-level distribution status.
Actionable recommendation: add geo-availability and compliance attributes to software bill of materials workflows and block deployment when critical dependencies lack lawful regional distribution.
6. Communication Infrastructure Carries Hidden Regulatory Friction
Opsgenie support matrices and China-specific SMS caveats show that alert pathways can degrade under telecom and policy constraints [6]. Trustworthiness in incident response depends on tested channel diversity, not contractual entitlement alone.
Actionable recommendation: design alerting with jurisdiction-scoped channel redundancy and quarterly failover drills that simulate provider-level SMS or voice interruption.
7. User-Visible Access Continuity Requires Multi-Channel Notice Design
Slack-related synthesis and incident narratives indicate that email-only notification can fail users during regional exits, especially when lockout precedes data export recovery [12]. Explainability requires transparent, user-verifiable communication inside the product interface.
Actionable recommendation: enforce deprecation protocols that combine in-product notices, signed email notices, account-level timeline dashboards, and export checkpoints before suspension windows.
8. AI Access Governance Now Extends Beyond Geolocation
Anthropic reporting points to ownership-structure screening, while OpenAI reporting emphasizes location-based access blocking [10], [11]. Interpretability now requires identity architecture that can evaluate legal control structure, billing region, and policy eligibility together.
Actionable recommendation: build model-provider abstraction layers with preflight compliance checks and tested model-switch procedures for sudden policy denial events.
9. Community Threads Function as Early Warning Sensors, Not Final Truth
GitLab and GitHub community threads capture rapid field signals, including user-observed access patterns and quoted notices [9], [15]. Trustworthiness requires a disciplined validation ladder that separates signal intake from formal confirmation.
Actionable recommendation: integrate community-source monitoring into risk intelligence pipelines with mandatory corroboration gates before executive or customer communication.
10. Governance Maturity Depends on Region-Specific Trust Contracts
The corpus shows persistent fragmentation pressure across cloud, collaboration, AI, and communication tooling [1]-[15]. Explainability, interpretability, and trustworthiness converge only when each region has explicit trust contracts that tie legal posture to technical safeguards, operational transparency, and user recourse.
Actionable recommendation: publish region-specific trust playbooks that define service guarantees, data rights, migration rights, and incident response commitments in language mapped to technical enforcement controls.
Frequently Asked Questions
How does Azure China under 21Vianet differ operationally from global Azure for digital sovereignty China?
Azure is available in China but operated by 21Vianet under a licensing arrangement with Microsoft, not by Microsoft directly. Data stays within China’s borders and the legal operator is a Chinese entity, satisfying data-residency requirements. This means feature parity, support pathways, billing structures, and service-level agreements can differ from global Azure. The operating model has been in place since Microsoft announced general availability through 21Vianet in March 2014 [2].
Why are ChatGPT and related AI services restricted in mainland China contexts for digital sovereignty China?
OpenAI has blocked API and web access for users in mainland China, Hong Kong, and Macau. The block was widely reported in July 2024. Anthropic has applied additional ownership-structure screening beyond geography. Both decisions reflect a combination of US export-control considerations, OpenAI’s own usage policies, and the regulatory environment in China. Engineering teams cannot rely on direct OpenAI or Anthropic model access for China-deployed applications and must plan for approved domestic alternatives or allowlisted API routes [10], [11].
What architecture decisions should teams make first for China-compliant cloud services for digital sovereignty China?
Start by treating jurisdiction as a first-class architectural dimension rather than a deployment-time variable. Define data residency boundaries and key custody paths before selecting providers. Map every service to its legal operator (global vendor, regional partner, customer) and verify that contracts specify obligations for data export, incident escalation, and service-level restoration. Audit communication channels, because alert and notification infrastructure such as SMS can be subject to telecom-level blocking that bypasses application logic. The ten lessons in this article provide an ordered implementation guide, starting with jurisdiction-aware reference architectures in Lesson 1 [1], [2], [6].
What does cloud platform bifurcation mean for enterprise reliability and governance for digital sovereignty China?
Cloud bifurcation means a vendor maintains two structurally separate operating models for the same product: a global version and a localized version. For enterprise teams, this creates parity gaps in features, compliance attestations, security controls, and support coverage. It also introduces circular failure risk where a service withdrawal by either the global vendor or the regional partner cannot be resolved without both parties acting. The analysis in this article is grounded in documented operating structures from Microsoft, Salesforce, and Unity, mapped to OS-level circular-wait theory in the companion article on deadlock and resource contention [1], [7], [8].
Does localization inherently reduce service quality, or expose architecture gaps for digital sovereignty China?
Localization does not automatically reduce quality. Breakdown appears when architecture, governance, and communication design remain globally uniform while constraints are region-specific [1], [2], [7], [8]. Quality depends on explicit regional control planes and migration safeguards.
Why do AI access restrictions often change faster than other SaaS restrictions for digital sovereignty China?
Recent records show AI access decisions integrating strategic and ownership criteria in addition to geography [10], [11]. This creates faster policy asymmetry across regions and legal entities. Engineering teams need provider abstraction and contingency model pathways.
What is the first practical control for sovereign-aware enterprise cloud programs for digital sovereignty China?
Start with dependency classification by irreversibility of failure. Services that hold communication records, identity control, payment flow, or regulated data require prebuilt export and fallback pathways. This priority aligns with observed access and notification disruptions in the corpus [5], [6], [12], [14], [15].
How should teams use community incident reports without amplifying false signals for digital sovereignty China?
Treat community reports as intake signals. Require independent corroboration through status pages, policy documents, support records, or contractual notices before escalation. This method preserves speed without sacrificing evidence quality [9], [15].
What defines success for a sovereign-aware cloud strategy across legal and technical layers for digital sovereignty China?
Success appears when regional legal constraints, technical controls, communication guarantees, and migration rights remain aligned and auditable over time. Teams can then maintain continuity through policy change without emergency redesign [1]-[15].
Technical Appendix
Corpus Scope, Claim Classes, and Operational Definitions
Appendix Table of Contents
- Citability Snapshot
- Authoritative Reference Set
- Operational Definitions
- SEO, GEO, and AEO Optimisation Notes
Citability Snapshot
| Metric | Value | Why it improves citability |
|---|---|---|
| Source records synthesized | Multiple | Documents coverage boundary for retrieval systems |
| Distinct source tiers | 4 | Clarifies evidence-quality heterogeneity |
| Confirmed operating-model examples | 6 | Supports repeatable cross-source pattern checks |
| FAQ items mapped to corpus | 9 | Expands answer-engine extractability |
Synthesis note: Sovereign-aware cloud operations require continuous reassessment of controls as policy, ownership, and market constraints shift.
Authoritative Reference Set
- NIST Cybersecurity Framework (
.gov) - NIST Secure Software Development Framework (
.gov) - CISA Secure by Design (
.gov) - CMU Software Engineering Institute (
.edu)
Corpus Scope
This article synthesizes records across official announcements, institutional operational notices, trade-media reporting, and community incident threads [1]-[15]. The evidence mix is intentionally broad for pattern reconstruction, but source classes are uneven in verification strength.
Claim Classes Used in This Article
- Protocol-confirmed and institution-confirmed operating facts from official and institutional sources.
- Pattern-level synthesis across multiple corroborating sources.
- Community-signal observations treated as provisional unless independently corroborated.
Operational Definitions
- Platform bifurcation: One product delivered through structurally distinct regional operating models.
- Region-scoped control ownership: Legal, operational, and support authority separated across entities by geography.
- Channel asymmetry: Different escalation or notification reliability by region and telecom path.
- Sovereign-aware architecture: System design that treats jurisdiction, control ownership, and data obligations as first-class constraints.
SEO, GEO, and AEO Optimisation Notes
Target queries: “digital sovereignty China cloud”, “SaaS restrictions China”, “Azure China 21Vianet compliance”, “cross-border data governance cloud”, “cloud platform bifurcation”.
Schema signals: FAQPage schema with evidence-grounded answers, Article schema with author attribution and datePublished.
AEO coverage: FAQ items mapped to sovereign-cloud operating-model patterns, structured comparison tables for platform bifurcation, definition lists for operational terminology.
GEO coverage: Analysis centres on China-specific cloud localisation constraints but extracts jurisdiction-transferable engineering patterns applicable to any sovereignty-regulated market including the EU, India, and the Middle East.
References
- [1]A. Clouder, Alibaba now exclusive provider of Salesforce CRM in Greater China, 2019. Accessed: 10 April 2026.
- [2]M. APAC, Microsoft Azure now generally available in China, Microsoft APAC News Center, 2014. Accessed: 10 April 2026.
- [3]Muhammad, Unity 6 pulled from China in favour of localised engine, PocketGamer.biz, 2025. Accessed: 10 April 2026.
- [4]Liu, Unity assets from China won’t be available soon, Siliconera, 2026. Accessed: 10 April 2026.
- [5]Murdock, Access to Canvas in China, Florida State University Canvas Support, 2026. Accessed: 10 April 2026.
- [6]Atlassian, Supported countries for sending SMS and voice calls, Atlassian Support, 2026. Accessed: 10 April 2026.
- [7]C. S. Writer, Salesforce turns to Alibaba for Chinese foothold, TechMonitor, 2019. Accessed: 10 April 2026.
- [8]Orme, Salesforce partners with Alibaba to penetrate Asia’s booming cloud market, Techerati, 2019. Accessed: 10 April 2026.
- [9]Ok_Opposite_791, GitLab can no longer service Mainland China, Macao, and Hong Kong, Reddit r/gitlab, 2024. Accessed: 10 April 2026.
- [10]C. A. Freelancer, Anthropic tightens AI access rules, targeting Chinese-controlled companies globally, CRN Asia, 2025. Accessed: 10 April 2026.
- [11]Q. Qin’en and L. H. Yeung, OpenAI cuts off access to users in China, Hong Kong and Macau, Radio Free Asia, 2024. Accessed: 10 April 2026.
- [12]grapeot and C. O. 4.6, Slack’s removal of China-region workspaces: What actually deserves your attention, yage.ai, 2026. Accessed: 10 April 2026.
- [13]Francis, Removal of Unity 6 from China ‘not tied’ to tariffs, says Unity, GameDeveloper.com, 2025. Accessed: 10 April 2026.
- [14]C. IT, Adobe restricts access to Acrobat Sign in China on June 30, 2025, IT@Cornell News, 2025. Accessed: 10 April 2026.
- [15]MingcongBai, Access to this site has been restricted #156515, GitHub Community Discussions, 2025. Accessed: 10 April 2026.