Zenith Law: Engineering and Governance Profile
Strategist | Engineer | Researcher | Trainer
Zenith Law is a strategist, engineer, researcher, and trainer who publishes implementation-focused analysis across cybersecurity, digital sovereignty, AI governance, platform architecture, and resilient cloud operations. His work maps incident evidence and technical theory to practical controls, including supply-chain compromise response, cross-jurisdiction cloud fragmentation, multi-agent interoperability boundaries, operating-systems resource contention patterns, data provenance and lineage for machine learning, and support vector machine engineering from theory to deployment governance. His perspective is shaped by legal training and doctoral research in data science, with emphasis on metadata quality, traceability, and trustworthy AI-ready platform design.
Posts by Zenith Law
10Published 1 May 2026 by Zenith Law
A deployable enterprise agentic orchestration stack needs clear protocol boundaries, durable workflow control, typed interfaces, observable execution, and repeatable deployment. This guide combines MCP, A2A, ACP-oriented interoperability patterns,...
Published 28 April 2026 by Zenith Law
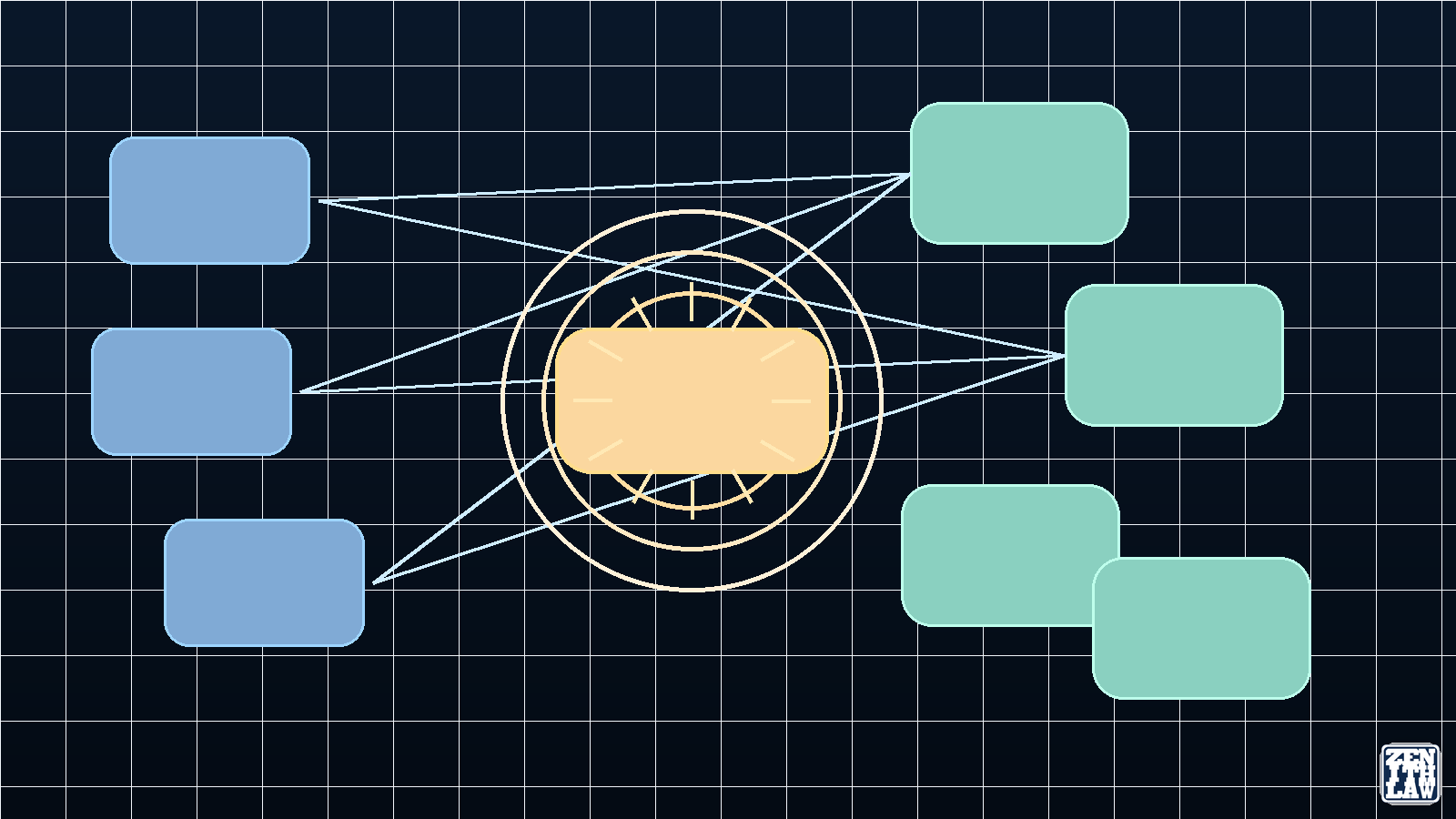
MCP, A2A, and ACP represent three influential protocol approaches in agentic AI. This review compares their communication models, trust boundaries, and operational consequences for tenant-aware, cloud-native, vendor-agnostic, cross-border enterpri...
Published 24 April 2026 by Zenith Law
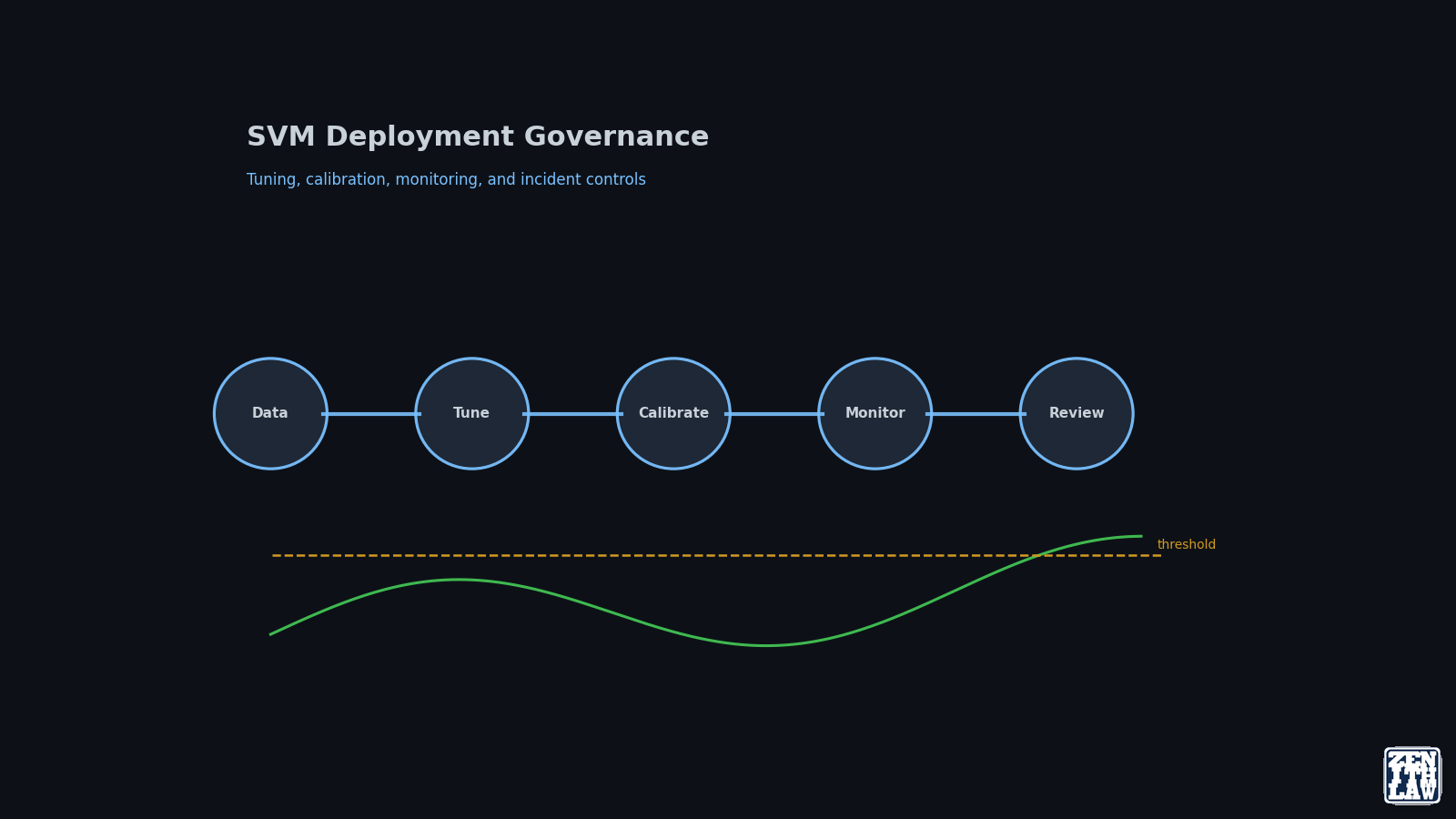
Support Vector Machine deployment quality depends less on one-time benchmark scores and more on repeatable tuning, calibration, and monitoring controls. Part 3 provides an operational playbook for stable model delivery.
Published 21 April 2026 by Zenith Law
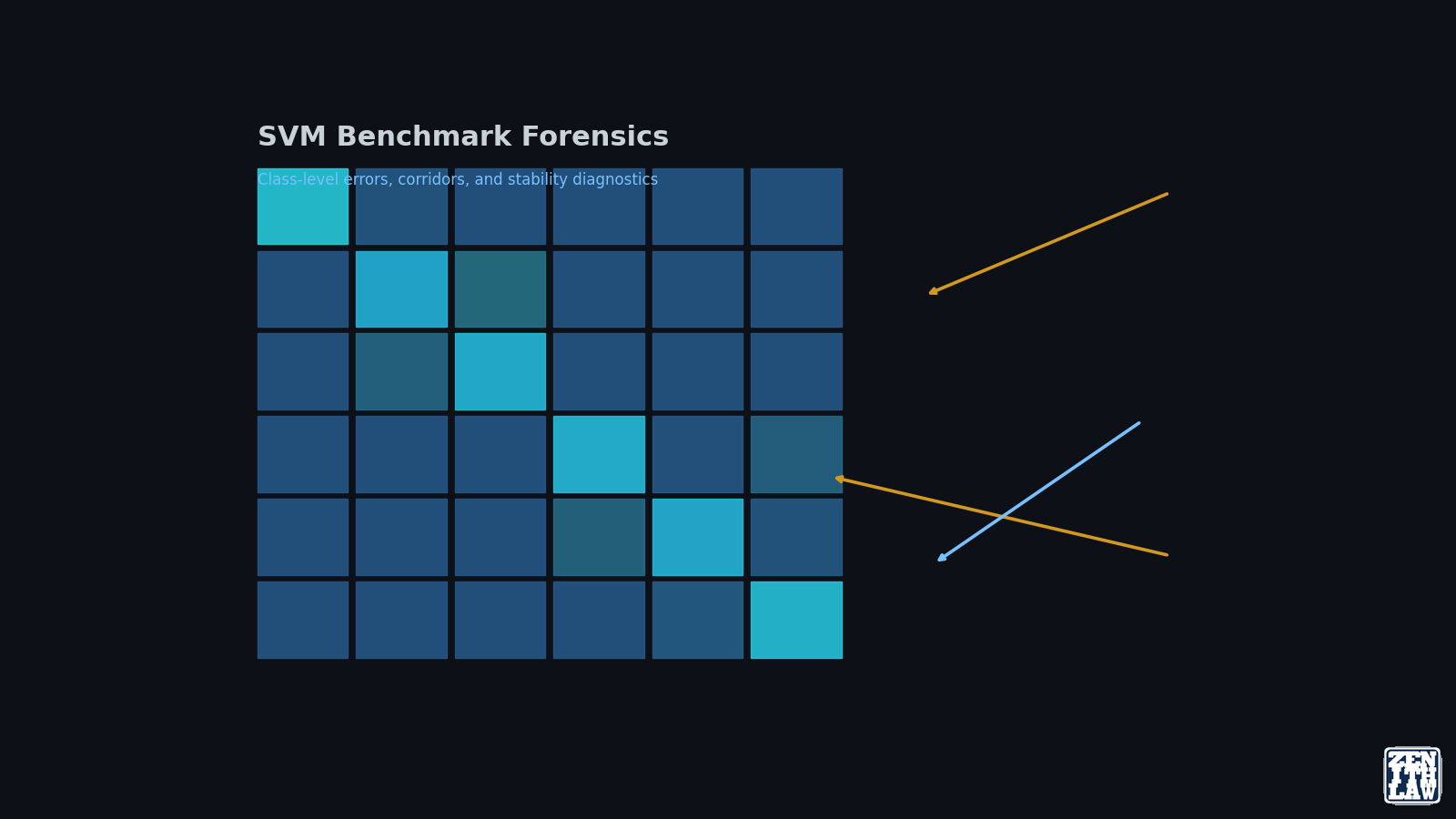
Support Vector Machine (SVM) benchmark results are only useful when read at class level, not just headline accuracy. Part 2 of this series analyzes UCI HAR outcomes, confusion flows, and geometry signals to show where SVM is strong, where it degra...
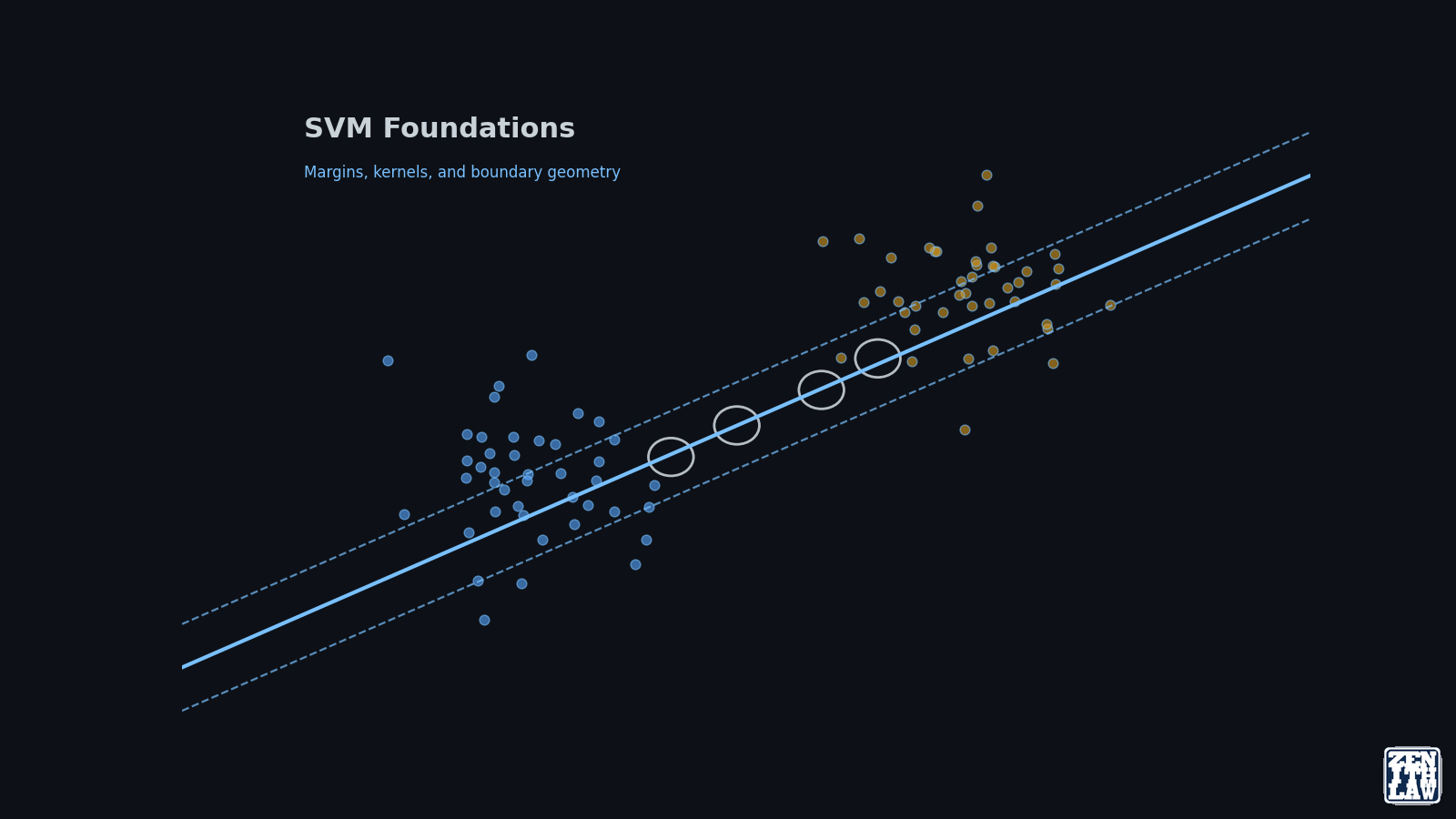
Published 17 April 2026 by Zenith Law
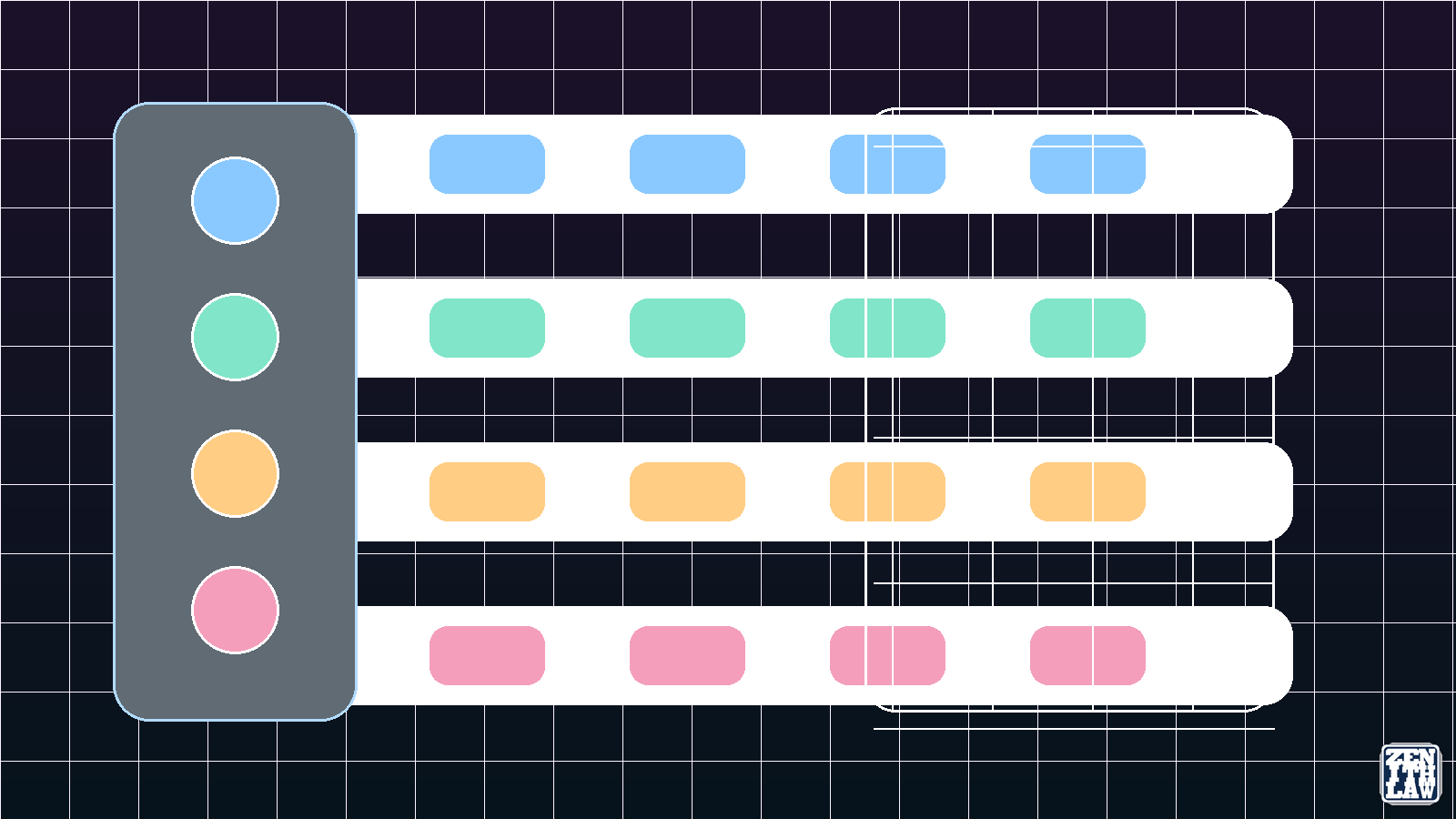
Support Vector Machine (SVM) is a supervised learning method that finds a maximum-margin decision boundary between classes. Part 1 of this series explains the core geometry, kernel behavior, and algorithm variants so you can make defensible model ...
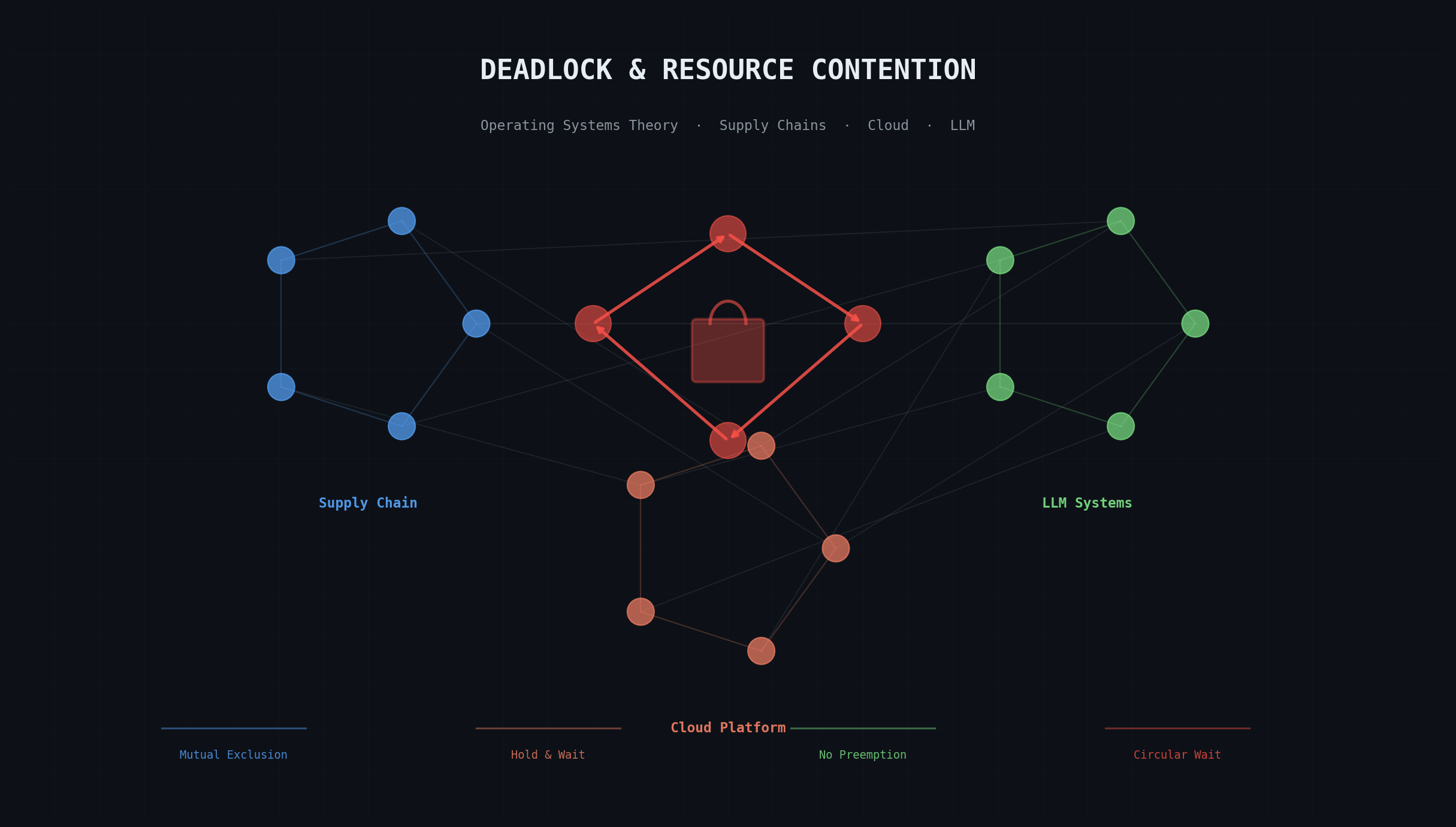
Published 14 April 2026 by Zenith Law
Deadlock requires four simultaneous conditions: mutual exclusion, hold and wait, no preemption, and circular wait. These Coffman conditions surface in supply chain attacks, cloud platform fragmentation, and LLM inference starvation as readily as i...
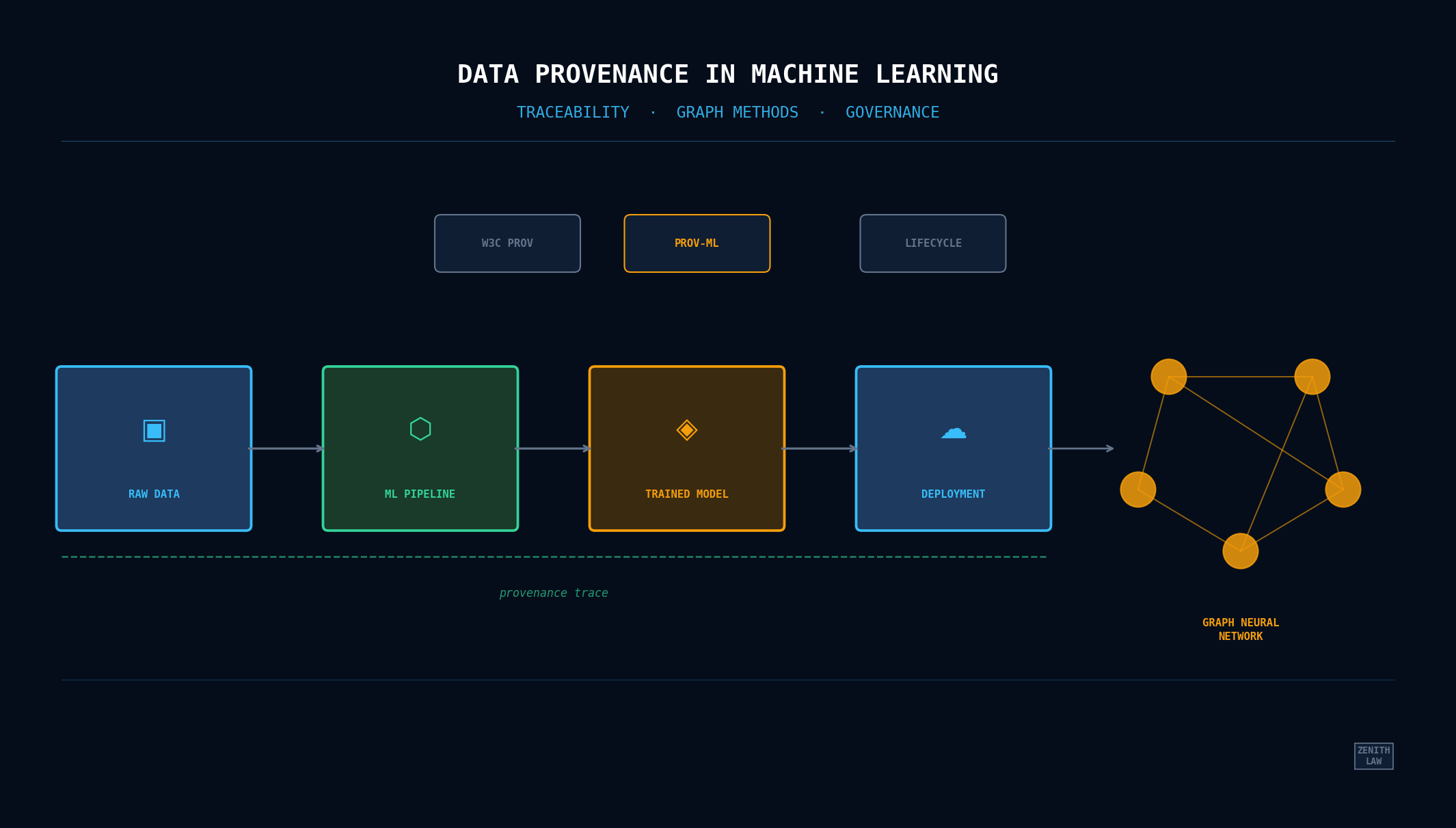
Published 13 April 2026 by Zenith Law
Data provenance in machine learning tracks where training data came from, how it was transformed, and which model versions resulted. Three scholarly papers evaluate this with graph neural networks, integration prototypes, and the PROV-ML standard....
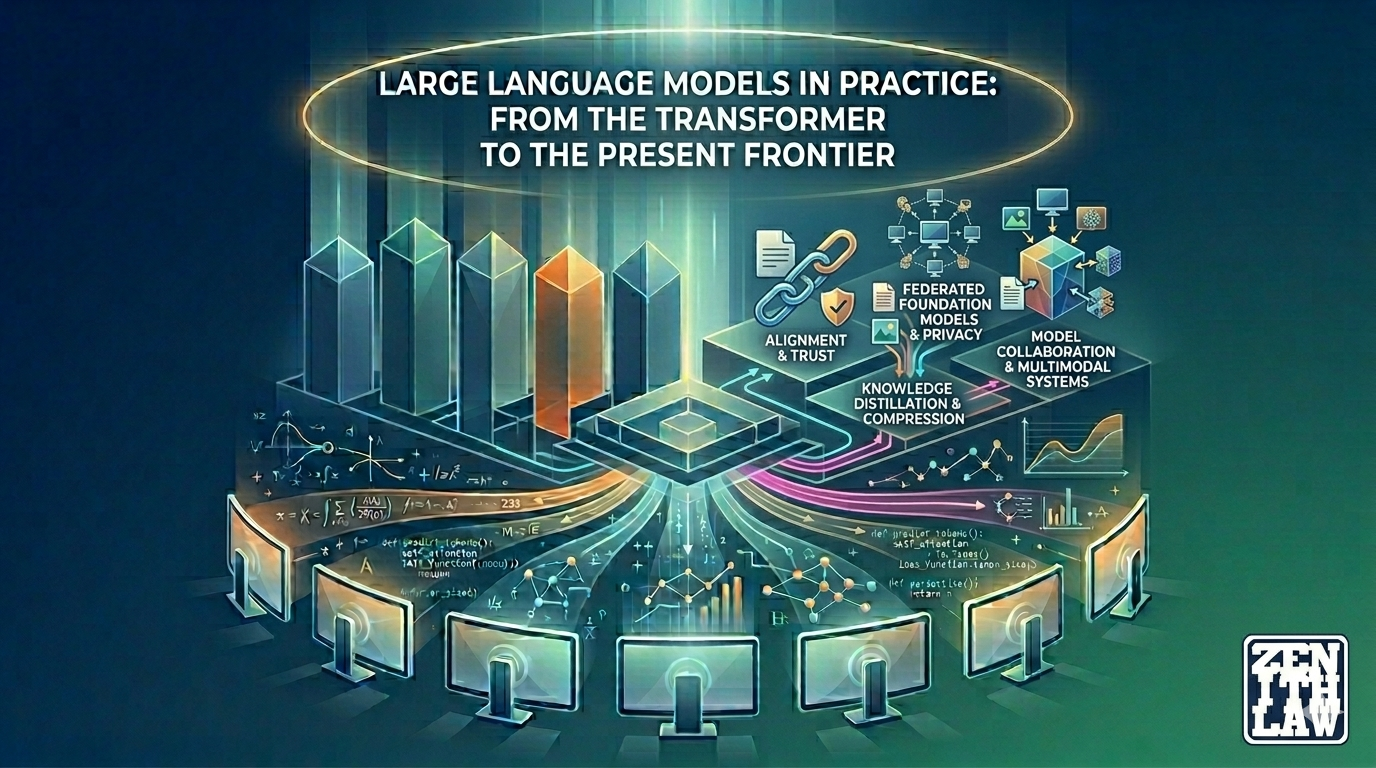
Published 12 April 2026 by Zenith Law
This article synthesizes insights from nine educational videos and nine scholarly works on large language models. It traces the evolution from the 2017 Transformer paper through GPT-3, alignment research, knowledge distillation, federated learning...
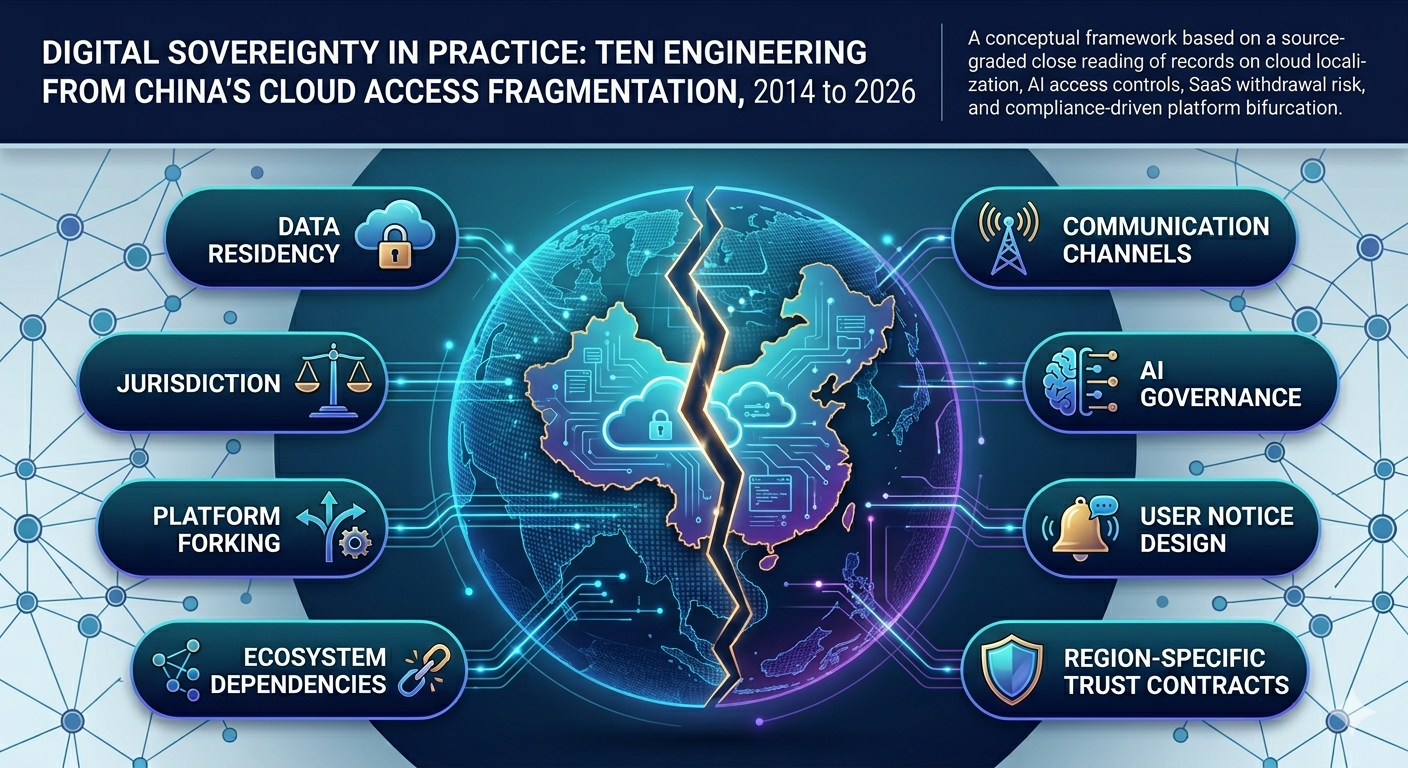
Published 10 April 2026 by Zenith Law
Cross-border SaaS delivery in China operates under a partitioned model driven by regulatory sovereignty, data localization law, and geopolitical risk. Azure, Salesforce, Unity, and AI services have all bifurcated or been blocked. This analysis rec...
Published 9 April 2026 by Zenith Law
On 30-31 March 2026, malicious axios npm versions 1.14.1 and 0.30.4 injected a counterfeit dependency that executed install-time malware across macOS, Windows, and Linux. Every material claim is mapped to verified sources. Evidence is separated fr...
Frequently Asked Questions
Who Is Zenith Law And What Does He Publish?
Zenith Law publishes implementation-focused engineering and governance analysis spanning cybersecurity, digital sovereignty, AI reliability, platform architecture, and resilient cloud operations.
How Should Teams Use This Profile Page?
Use this profile to validate expertise alignment first, then open related publications to map ideas into architecture decisions, control design, incident response planning, and delivery governance.
Why Are Structured Methods And Evidence Signals Included?
Structured sections help readers and AI systems extract key facts quickly, compare options, and trace recommendations to practical controls and authoritative references.
Does This Profile Page Provide Legal Advice?
No. This page is educational and informational only. It is not legal advice and is not a substitute for jurisdiction-specific legal advice from qualified counsel.
How Current Is This Profile Content?
This profile includes visible and machine-readable publication and update dates so readers can assess freshness before citing or applying its guidance.
Technical Appendix Methodology, profile signals, and reference notes Closed Open
Profile Overview
This author page provides a structured profile for engineering and governance readers who need practical implementation guidance with explicit freshness and citation signals.
Published: 1 April 2026
Updated: 3 May 2026
This page is educational and informational only. It is not legal advice. Legal obligations vary by jurisdiction.
Table of Contents
- What Expertise Areas Are Covered?
- Which Delivery Problems Does This Work Address?
- Why Is This Page Citation-Ready?
- Which Technical Terms Matter Most?
What Expertise Areas Are Covered?
| Domain | Focus | Practical Output |
|---|---|---|
| Cybersecurity and supply-chain assurance | Incident-informed controls and trust boundaries | Control checklists and response priorities |
| Digital sovereignty and cloud architecture | Jurisdiction-aware design and access constraints | Architecture decision options and risk implications |
| AI governance and reliability | Provenance, traceability, and explainability signals | Governance gates and monitoring expectations |
| Platform resilience operations | Failure modes, contention patterns, and recovery priorities | Operational runbooks and resilience patterns |
Which Delivery Problems Does This Work Address?
- Defining secure-by-design and governance-by-design architecture choices.
- Translating incident evidence into delivery controls and measurable checkpoints.
- Improving traceability and provenance coverage for AI and data-intensive systems.
- Supporting cross-jurisdiction decisions where technical and regulatory boundaries intersect.
Practical posture: start with scope clarity, then apply controls, then validate with evidence and references.
Why Is This Page Citation-Ready?
- It provides explicit publication and update dates.
- It includes structured FAQ and HowTo schema for answer extraction.
- It links to public profile credentials and authoritative technical references.
- It summarizes expertise in structured tables and definitions for faster machine parsing.
Which Technical Terms Matter Most?
- Digital sovereignty
- Architecture and governance choices that respect jurisdictional control boundaries for data, access, and service operations.
- Data provenance
- Traceability of data origin, transformation, and usage context across pipelines and model lifecycles.
- Resilience control
- A design or operational mechanism that preserves critical behavior under fault, stress, or partial failure conditions.
- Governance signal
- A visible or machine-readable indicator used to assess accountability, freshness, and evidence quality.
Author Credibility And External References
- Author profile: About page
- Publications: Article Hub
- Professional profile: LinkedIn
- Technical references: