MCP, A2A, and ACP represent three influential protocol approaches in agentic AI. This review compares their communication models, trust boundaries, and operational consequences for tenant-aware, cloud-native, vendor-agnostic, cross-border enterprise systems with human-in-the-loop orchestration.
Introduction
Agentic AI systems are pushing enterprise software toward large-scale distributed coordination among models, tools, services, and humans. In that shift, protocol boundaries now shape delivery speed, operational risk, and cross-vendor interoperability as much as model quality.
Model Context Protocol (MCP) standardizes model-to-capability access [1], [2]. Agent2Agent (A2A) standardizes peer-agent collaboration with task lifecycle semantics [3], [4]. Agent Communication Protocol (ACP) introduced a REST-oriented agent interoperability model with async-first behavior, discovery, and multimodal messaging [5], [6].
ACP is historically important in this comparison and still useful for architecture reasoning. It is also in transition. As of May 2026, ACP maintainers publicly described merger work into A2A under Linux Foundation collaboration, with migration guidance for existing ACP adopters [7], [8].
Scope and Method
This review compares MCP, A2A, and ACP against enterprise deployment constraints rather than protocol marketing claims. Source inputs include official specifications, protocol documentation, ACP OpenAPI materials, and ACP-to-A2A transition notices [2], [3], [6], [7].
Comparison dimensions:
- Communication model and state semantics.
- Discovery and capability advertisement.
- Security and trust boundaries.
- Human-in-the-loop and practical HCI implications.
- Tenant-aware, cross-border, vendor-agnostic cloud operation.
This post is informational and technical in nature and is not legal advice.
Three claim classes are used throughout:
- Protocol-confirmed claims are stated directly in the public specifications or official protocol documentation.
- Implementation-oriented synthesis connects those protocol details to practical system design choices.
- Critical evaluation highlights where a protocol is a poor fit even when it is technically possible to make it work.
MCP in Practical Terms
MCP is a model-to-capability integration protocol. It uses JSON-RPC 2.0 between hosts, clients, and servers, and it treats servers as providers of resources, prompts, and tools. Clients can additionally expose sampling, roots, and elicitation features to servers [2]. The core design question is: what capabilities should the model-facing application make available to the model, under explicit user control?
That design becomes clearer when the primitives are separated:
- Resources are contextual data surfaces. They behave like safe, inspectable inputs to model reasoning.
- Prompts are reusable interaction templates and workflows.
- Tools are executable capabilities that may produce side effects and therefore require sharper consent and safety controls.
The specification reinforces that separation with explicit security principles: user consent, privacy protection, tool safety, and approval for sampling requests are all first-order requirements, not optional UX polish [2]. In other words, MCP assumes that exposing capabilities to an LLM is powerful enough to deserve a protocol-level safety posture.
A2A in Practical Terms
A2A is a peer-agent collaboration protocol. It focuses on discovery, task creation, streaming updates, push notifications, multi-turn continuation, authenticated capability disclosure, and artifact delivery between independent agents [3]. Its primary design question is different from MCP’s: how should one autonomous system coordinate with another autonomous system without needing to reveal internal reasoning, memory, or tool implementation?
The official specification makes that posture explicit. A2A treats the Task as the central unit of work, uses Messages for communication turns, uses Artifacts for task outputs, and uses the Agent Card as the discovery manifest that advertises supported interfaces, skills, security schemes, and optional capabilities such as streaming, push notifications, and extended cards [3]. That gives A2A a stronger built-in story for long-running work than MCP.
The protocol is also intentionally async-first. A task may complete immediately, continue in the background, pause in TASK_STATE_INPUT_REQUIRED, or move into TASK_STATE_AUTH_REQUIRED while another human or agent resolves authorization [3]. That makes A2A structurally well-suited to collaborative service workflows, approval chains, and multi-agent delegation trees.
ACP in Practical Terms
ACP defines a RESTful, agent-to-agent communication approach with synchronous, asynchronous, and streamed execution patterns, plus agent discovery and stateful or stateless run models [5], [6].
Practically, ACP offered three useful properties for enterprise teams:
- HTTP-native integration ergonomics for platform teams that already standardize on REST gateways.
- A structured run lifecycle and agent manifest approach in an OpenAPI-described protocol surface.
- A vendor-neutral interoperability framing that addressed framework fragmentation and cross-organization coordination.
Current status matters for architecture choices. As of May 2026, ACP contributors publicly announced active convergence into A2A, so long-lived greenfield planning should factor migration and standards consolidation into roadmap decisions [7], [8].
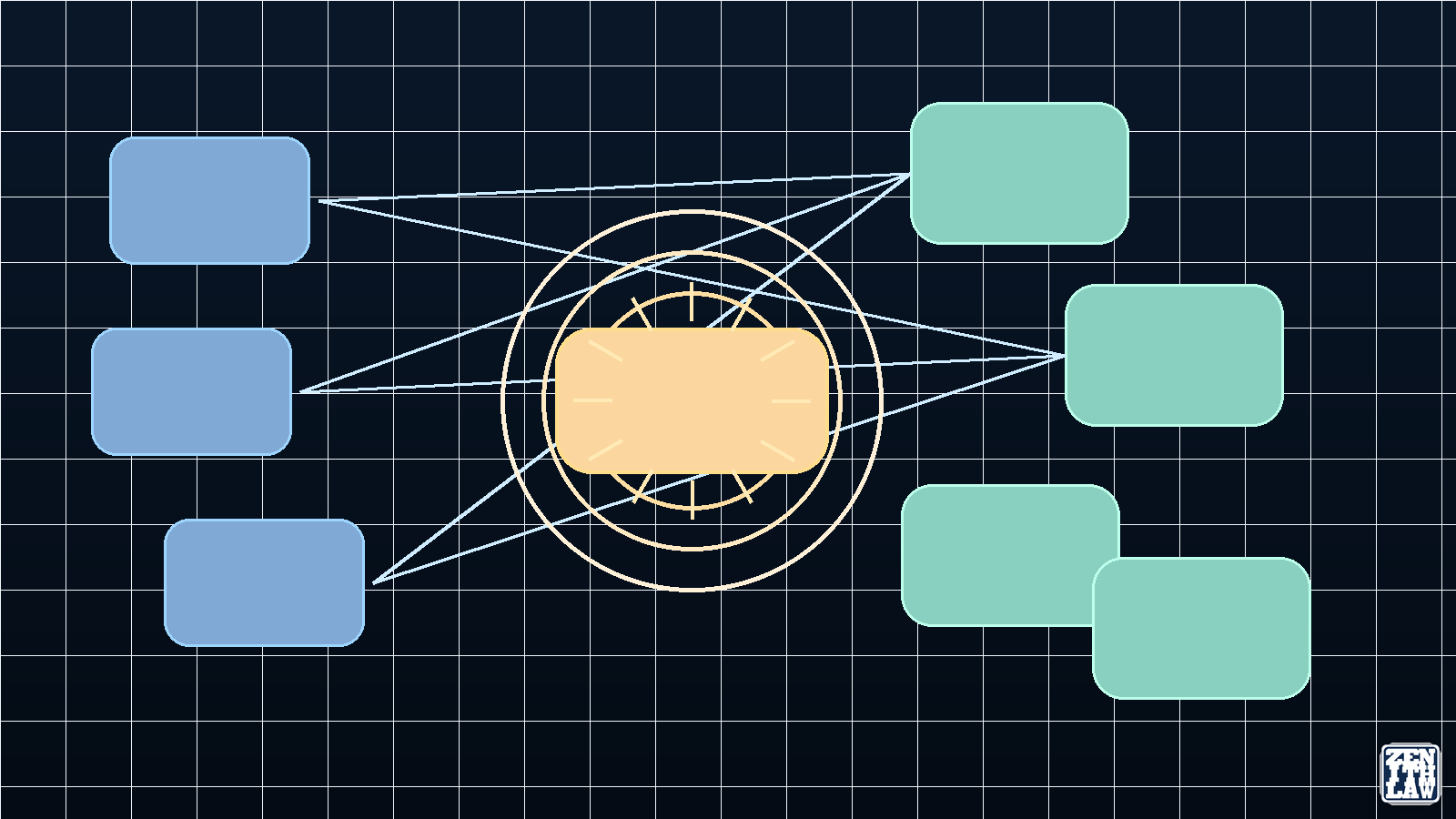
Scope of Comparison: Capability Bus, Task Bus, or REST Interop Bus
The clearest design question is not “which protocol is the best.” The question is “which interaction boundary are you standardizing.”
| Dimension | MCP | A2A | ACP |
|---|---|---|---|
| Primary boundary | Model-to-tools/resources/prompts | Agent-to-agent task collaboration | REST-based agent interoperability |
| Core abstraction | Capability invocation | Task, message, artifact lifecycle | Agent manifest, run lifecycle, events |
| Typical transport style | JSON-RPC patterns | Protocol-defined agent task interfaces | HTTP/REST with OpenAPI-described endpoints |
| Async and long-run handling | Possible, host-dependent | First-class | First-class |
| Discovery surface | Exposed server capabilities | Agent Card | Agent manifest and discovery endpoints |
| HCI implication | High need for approval UX around tools | High need for task-progress UX and handoff visibility | High need for run-status UX and predictable HTTP semantics |
| Current standards trajectory | Active | Active | Converging toward A2A collaboration path |
This framing allows balanced architecture decisions without collapsing three different design intents into one layer.
Where MCP Is the Better Fit
MCP is usually the better fit when the remote surface is deterministic enough that the caller should experience it as a bounded capability rather than an independent partner.
Typical cases include:
- A coding agent needs filesystem access, a browser automation tool, and a deployment command surface.
- A research assistant needs a retrieval layer, a citation formatter, and a structured report prompt.
- A support copilot needs CRM records, knowledge-base retrieval, and ticket-creation actions.
The architectural strength here is tight control. The host application can decide what to expose, how to describe it, when to request approval, and how much server visibility to permit during sampling or elicitation [2]. If a system owner wants a narrow capability envelope with explicit guardrails, MCP is usually the cleaner choice.
Where A2A Is the Better Fit
A2A is usually the better fit when the remote surface is autonomous enough that it should own its own execution strategy, task state, and multi-turn interaction loop.
Typical cases include:
- A planning agent delegates vendor onboarding to a compliance agent that may require documents, approvals, and asynchronous review.
- A travel orchestration agent coordinates a flight agent, hotel agent, and expense-policy agent, each with different state and response timing.
- An enterprise operations agent delegates investigation work to a specialist incident agent and subscribes to progress updates until the artifact set is complete.
These cases are awkward if reduced to simple tool calls. Once the remote side needs its own lifecycle, partial results, artifact streams, or authenticated extended metadata, the A2A task model becomes materially more expressive than a tool-only abstraction [3].
Where ACP Patterns Still Matter
ACP patterns remain valuable when teams need:
- REST-native agent integration through existing API gateways and service governance controls.
- OpenAPI-documented run endpoints that align with established enterprise integration practices.
- Lightweight interoperability patterns in mixed stacks that prioritize HTTP conventions over protocol-specific runtime adapters.
For greenfield strategy, this usually means preserving ACP design lessons while planning to interoperate with current A2A direction where standards convergence is already underway [7].
Common Design Mistakes
Mistake 1: Treating agents as tools by default
This usually looks attractive at prototype stage because a single tool call appears simpler than an agent handshake. The cost arrives later. The caller now has to invent task IDs, retries, continuation semantics, progress handling, artifact chunking, and permission boundaries that A2A already models natively.
Mistake 2: Treating simple tools as mini-agents
This introduces the opposite problem. If a remote action is basically “query this API” or “run this transformation,” wrapping it in agent discovery, task tracking, and peer negotiation can add latency and cognitive overhead without adding meaningful autonomy.
Mistake 3: Ignoring different trust boundaries
MCP’s safety model centers on user consent and careful exposure of capabilities to the model-facing host [2]. A2A’s safety model centers on authenticated inter-agent communication, scoped data access, task authorization, and secure push delivery [3]. These are related, but they are not interchangeable. A system that merges them carelessly can end up weak in both places.
Enterprise Architecture Considerations
Tenant-aware operation
Protocol selection should support tenant isolation, policy partitioning, and auditable boundary controls:
- MCP layer: tenant-scoped tool access and consent controls.
- A2A layer: tenant-aware delegation and task authorization.
- ACP/REST layer: tenant-aware run metadata and endpoint governance under API gateway controls.
Cloud-native and scalable deployment
In high-scale systems, protocol fit influences backpressure strategy, retry semantics, and observability cardinality. Practical design should include:
- Explicit idempotency keys for agent runs and delegated tasks.
- Stream-aware timeout tiers for interactive versus background tasks.
- Trace correlation IDs propagated across protocol boundaries.
Vendor-agnostic and cross-border collaboration
In many cross-border enterprise deployments, teams should assess jurisdiction-specific legal and contractual constraints, such as transfer mechanisms, localization obligations, and auditability requirements, and align identity architecture accordingly. Protocol design should not assume one cloud, one identity provider, or one legal region.
- Keep protocol contracts jurisdiction-neutral and policy-driven.
- Apply data residency and transfer controls at storage and transport boundaries where required by applicable law, regulation, customer contract, or internal policy.
- Maintain pluggable identity and key management patterns for multi-cloud and multi-region operations.
Human-in-the-Loop and HCI Considerations
Human-computer interaction quality is a protocol-level concern in agentic systems:
- MCP-centered workflows need clear approval surfaces before tool side effects.
- A2A-centered workflows need visible task state transitions, pause/resume controls, and ownership visibility.
- ACP/REST-centered workflows need predictable run-state feedback and error semantics that non-expert operators can interpret.
Operationally, effective HCI patterns reduce unsafe automation, lower mean-time-to-understanding during incidents, and improve user trust in autonomous workflows.
Practical Decision Framework
Use this rule set when choosing MCP, A2A, ACP, or hybrid layering:
- Choose MCP for model-facing capability access with explicit consent and policy controls.
- Choose A2A for multi-agent task collaboration with durable lifecycle semantics.
- Choose ACP-style REST contracts when HTTP-native interoperability and API-governed integration are dominant constraints.
- Choose hybrid layering when agents collaborate with peers and also need controlled tool access.
- Avoid single-protocol absolutism in enterprise systems spanning multiple teams, clouds, and jurisdictions.
A Combined Architecture Is Usually the Strongest Outcome
A common production pattern is layered, not exclusive. A front-door orchestrator or user-facing assistant communicates with specialist agents over A2A, each specialist uses MCP internally for tools and context, and REST-compatible ACP-style interfaces can bridge legacy integration surfaces where needed.
The companion article on building agentic orchestration with MCP, A2A, LangGraph, and LangChain turns this comparison into a concrete open-source stack, testing plan, and deployment blueprint.
Ten Learning Points
- MCP, A2A, and ACP address different interoperability layers.
- MCP is the strongest for controlled model-to-capability access.
- A2A is the strongest for autonomous peer-agent task orchestration.
- ACP contributes useful REST-oriented interoperability patterns and run semantics.
- Standards trajectory matters for roadmap risk, not only current feature lists.
- Tenant-aware policy partitioning should be protocol-aware, not bolted on later.
- Cross-border deployments require identity, data residency, and audit alignment across protocol boundaries.
- Human-in-the-loop UX quality directly impacts operational safety and trust.
- Hybrid layering usually outperforms protocol monoculture in enterprise settings.
- Protocol choice should be judged by lifecycle cost, observability quality, and migration resilience.
Glossary
Agent Card
The A2A discovery document that advertises an agent’s interfaces, skills, capabilities, and authentication requirements [3].
Artifact
An A2A task output object. It is distinct from conversational messages so clients can treat results as durable outputs rather than transient chat turns [3].
Resource
An MCP primitive used to expose contextual data for model consumption, generally without side effects [2].
Tool
An MCP primitive used to expose executable capability to an AI system. Tool execution should be treated as safety-sensitive [2].
Task
The central A2A unit of work. Tasks carry state, optional history, and artifacts, and can be updated through polling, streaming, or push notifications [3].
Agent Manifest
An ACP-oriented discovery artifact describing agent identity, capabilities, content types, and metadata for interoperable routing and integration [6].
Frequently Asked Questions
What is the main difference among MCP, A2A, and ACP?
MCP connects models or hosts to tools, resources, and prompts. A2A connects autonomous agents through task lifecycle collaboration. ACP defines a REST-oriented agent interoperability model with manifest and run semantics [2], [3], [6].
Is ACP obsolete now that it is converging with A2A?
ACP remains important for architecture learning and for existing deployments. New strategy should account for announced convergence and migration direction toward A2A to reduce future integration churn [7], [8].
Can MCP replace A2A in a multi-agent system?
Only in narrow cases. If the “other agent” is really acting like a stateless or tightly bounded capability, MCP can be sufficient. Once the remote side owns task state, asynchronous progress, artifact delivery, or agent discovery, A2A is usually the cleaner protocol fit.
Can A2A replace MCP for tool use?
It can, but it is usually wasteful. Simple tools do not benefit much from peer-agent ceremony. A2A shines when the remote side behaves like a collaborator, not just a callable capability.
When should I use both MCP and A2A together?
Use both when agents collaborate across system boundaries, but each agent still needs structured tool and data access within its own execution environment. That is the most common production-grade pattern.
How should enterprises handle cross-border and tenant-aware agent orchestration?
Use protocol layering with explicit tenant policy boundaries, jurisdiction-aware data controls, and portable identity patterns. Keep integration contracts vendor-agnostic and preserve audit trails across all delegated tasks and tool invocations.
Is MCP more secure than A2A?
Neither is universally “more secure.” They protect different boundaries. MCP emphasizes user consent, privacy, and tool safety for model-facing capability exposure. A2A emphasizes authenticated agent discovery, scoped task access, secure push delivery, and authorization across collaborating services [2], [3].
Do these recommendations apply identically across UK, EU, US, Canada, Hong Kong, China, and Australia?
No. Privacy, transfer, and sector-specific obligations vary by jurisdiction and industry. Treat protocol guidance as architecture input and confirm legal and regulatory requirements for the specific operating context.
What should teams prototype first when they are unsure?
Prototype the smallest honest boundary. Start with MCP if you are exposing a concrete capability. Start with A2A if you are delegating work to another service that owns its own lifecycle. If the boundary is still ambiguous, model the remote side’s expected autonomy before choosing a protocol.
Conclusion
The useful comparison is not “which protocol wins.” The useful comparison is “which interaction boundary is being standardized for your enterprise context.” MCP standardizes controlled capability access, A2A standardizes peer-agent collaboration, and ACP contributes REST-oriented interoperability patterns that remain relevant during standards convergence. Systems that preserve these boundaries while designing for tenant awareness, cloud-native scale, vendor neutrality, cross-border operation, and human-in-the-loop clarity are better positioned for resilient agentic AI adoption.
References
- [1]Model Context Protocol, What is the Model Context Protocol (MCP)?, Model Context Protocol documentation, 2026. Accessed: 28 April 2026.
- [2]Model Context Protocol, Specification, Model Context Protocol specification, 2026, Schema revision 2025-11-25. Accessed: 28 April 2026.Schema revision 2025-11-25
- [3]A2A Protocol Working Group, Agent2Agent (A2A) Protocol Specification, A2A Protocol v1.0.0, 2026. Accessed: 28 April 2026.
- [4]A2A Protocol Working Group, A2A and MCP: Detailed Comparison, A2A Protocol documentation, 2026. Accessed: 28 April 2026.
- [5]Agent Communication Protocol, Welcome, ACP documentation, 2026. Accessed: 28 April 2026.
- [6]Agent Communication Protocol, ACP OpenAPI specification, ACP documentation, 2026, OpenAPI 3.1.1 (version 0.2.0). Accessed: 28 April 2026.OpenAPI 3.1.1 (version 0.2.0)
- [7]i-am-bee maintainers, ACP Joins Forces with A2A Under the Linux Foundation, i-am-bee Discussions, 2025. Accessed: 28 April 2026.
- [8]S. Besen and A. Gutowska, What is Agent Communication Protocol (ACP)?, IBM Think, 2026, IBM page states ACP has merged with A2A and advises migration-path review. Accessed: 28 April 2026.IBM page states ACP has merged with A2A and advises migration-path review
- [9]A2A Project, Agent2Agent (A2A) Protocol, GitHub repository README, 2026. Accessed: 28 April 2026.
Continue Reading in This Series
These linked articles extend the same evidence trail and improve navigability for readers and search systems.
- Building Agentic Orchestration with MCP, A2A, LangGraph, and LangChain
- Data Provenance in Machine Learning: Traceability, Graph Methods, and Governance Lessons
- Deadlock and Resource Contention: Operating Systems Theory Applied to Supply Chains, Cloud Platforms, and LLM Systems
- Large Language Models in Practice: From the Transformer to the Present Frontier