Articles
Filter by tags and categories inside each card, and page through the full archive from this dedicated article hub.
10 published posts
Published 1 May 2026 by Zenith Law
A deployable enterprise agentic orchestration stack needs clear protocol boundaries, durable workflow control, typed interfaces, observable execution, and repeatable deployment. This guide combines MCP, A2A, ACP-oriented interoperability patterns,...
Published 28 April 2026 by Zenith Law
MCP, A2A, and ACP represent three influential protocol approaches in agentic AI. This review compares their communication models, trust boundaries, and operational consequences for tenant-aware, cloud-native, vendor-agnostic, cross-border enterpri...
Published 24 April 2026 by Zenith Law
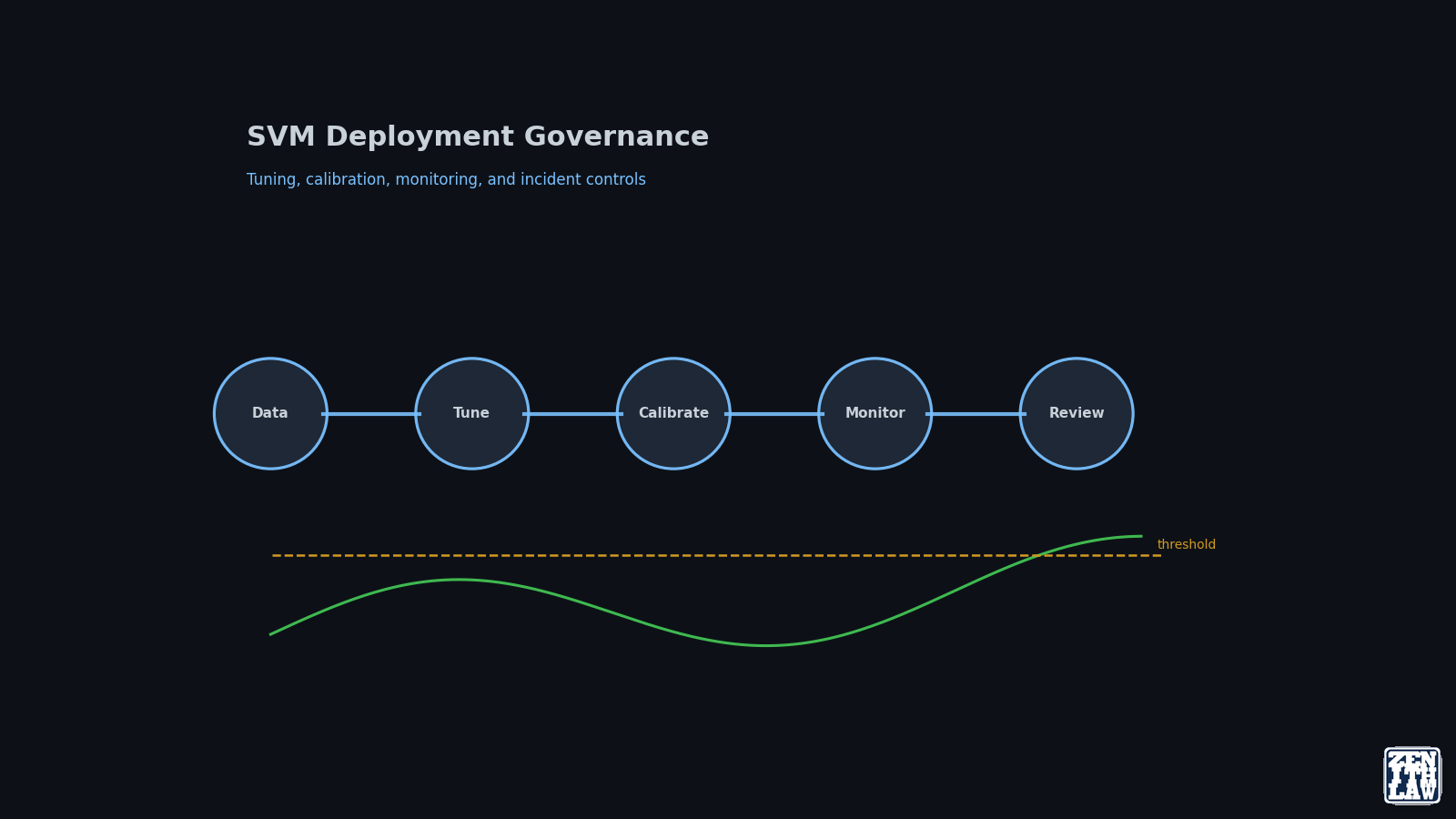
Support Vector Machine deployment quality depends less on one-time benchmark scores and more on repeatable tuning, calibration, and monitoring controls. Part 3 provides an operational playbook for stable model delivery.
Published 21 April 2026 by Zenith Law
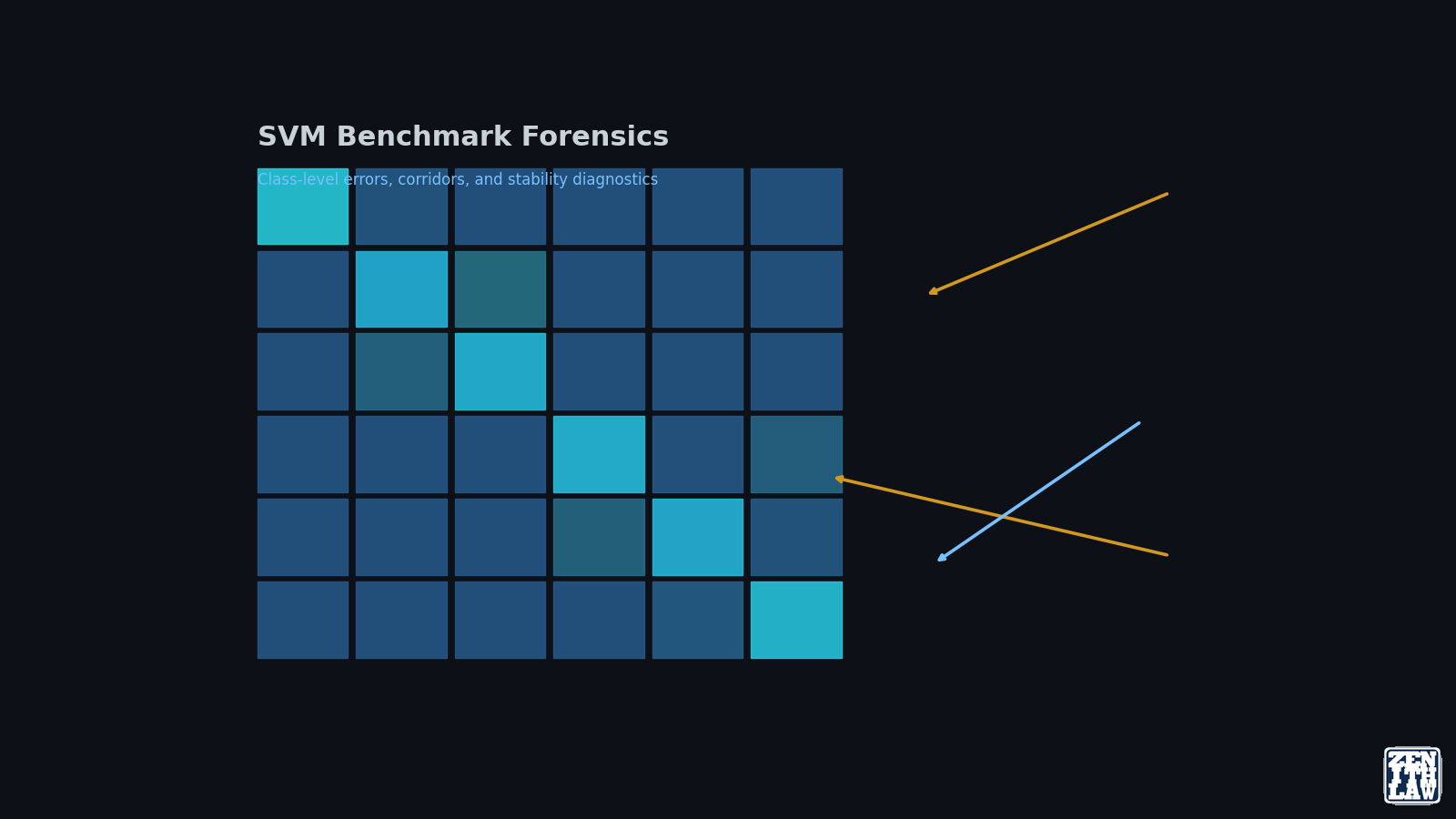
Support Vector Machine (SVM) benchmark results are only useful when read at class level, not just headline accuracy. Part 2 of this series analyzes UCI HAR outcomes, confusion flows, and geometry signals to show where SVM is strong, where it degra...
Published 17 April 2026 by Zenith Law
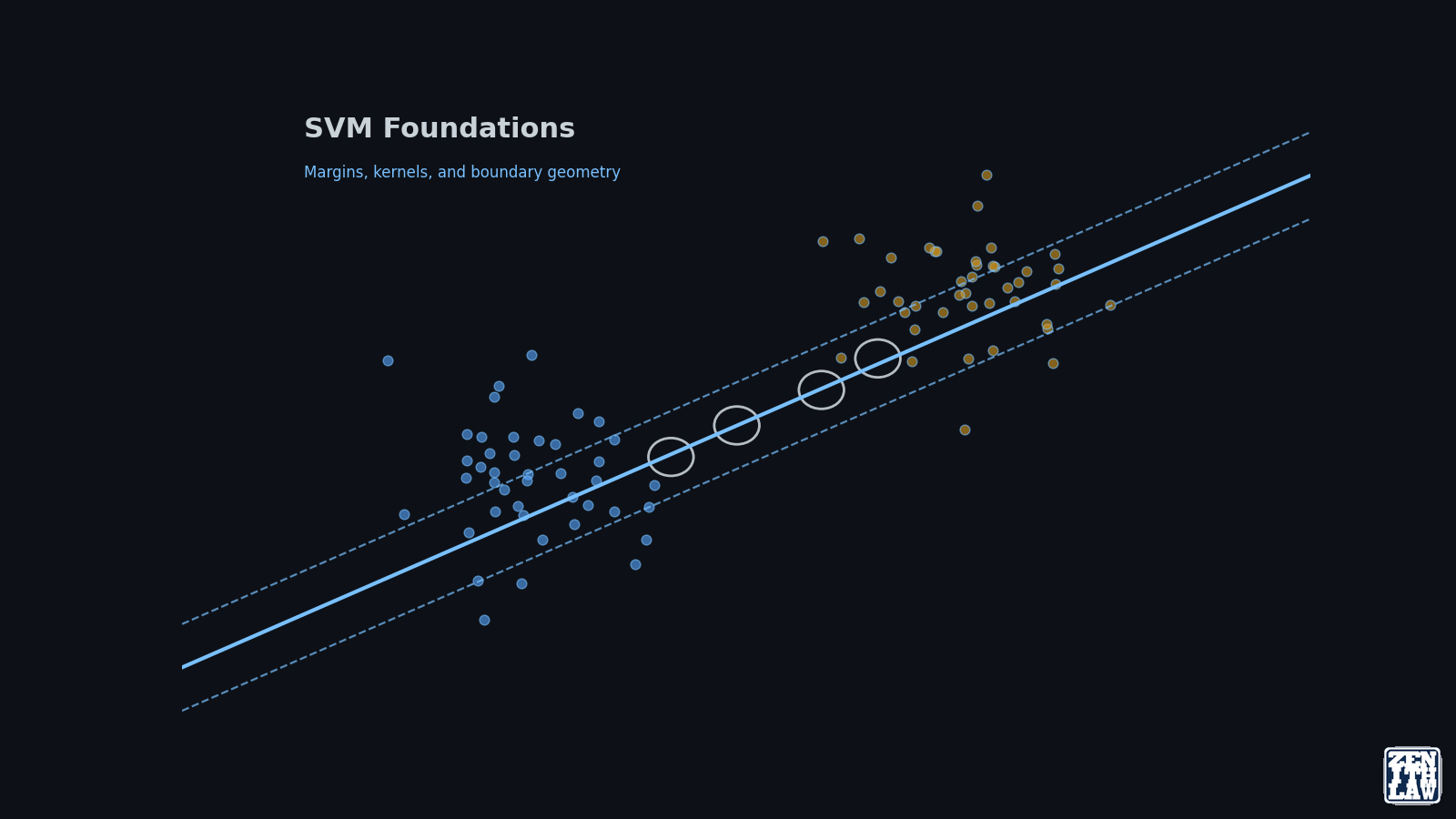
Support Vector Machine (SVM) is a supervised learning method that finds a maximum-margin decision boundary between classes. Part 1 of this series explains the core geometry, kernel behavior, and algorithm variants so you can make defensible model ...
Published 14 April 2026 by Zenith Law
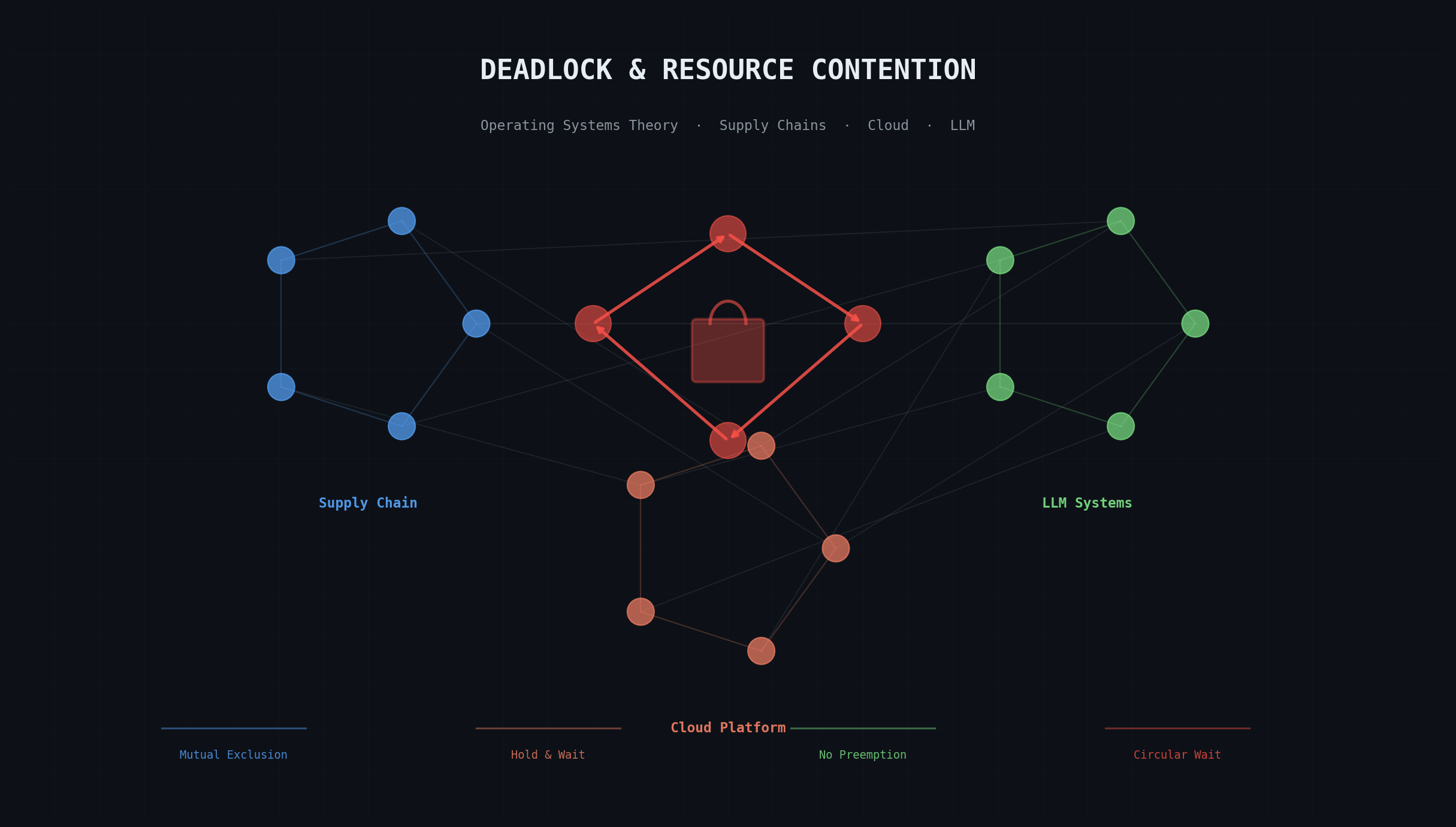
Deadlock requires four simultaneous conditions: mutual exclusion, hold and wait, no preemption, and circular wait. These Coffman conditions surface in supply chain attacks, cloud platform fragmentation, and LLM inference starvation as readily as i...
Published 13 April 2026 by Zenith Law
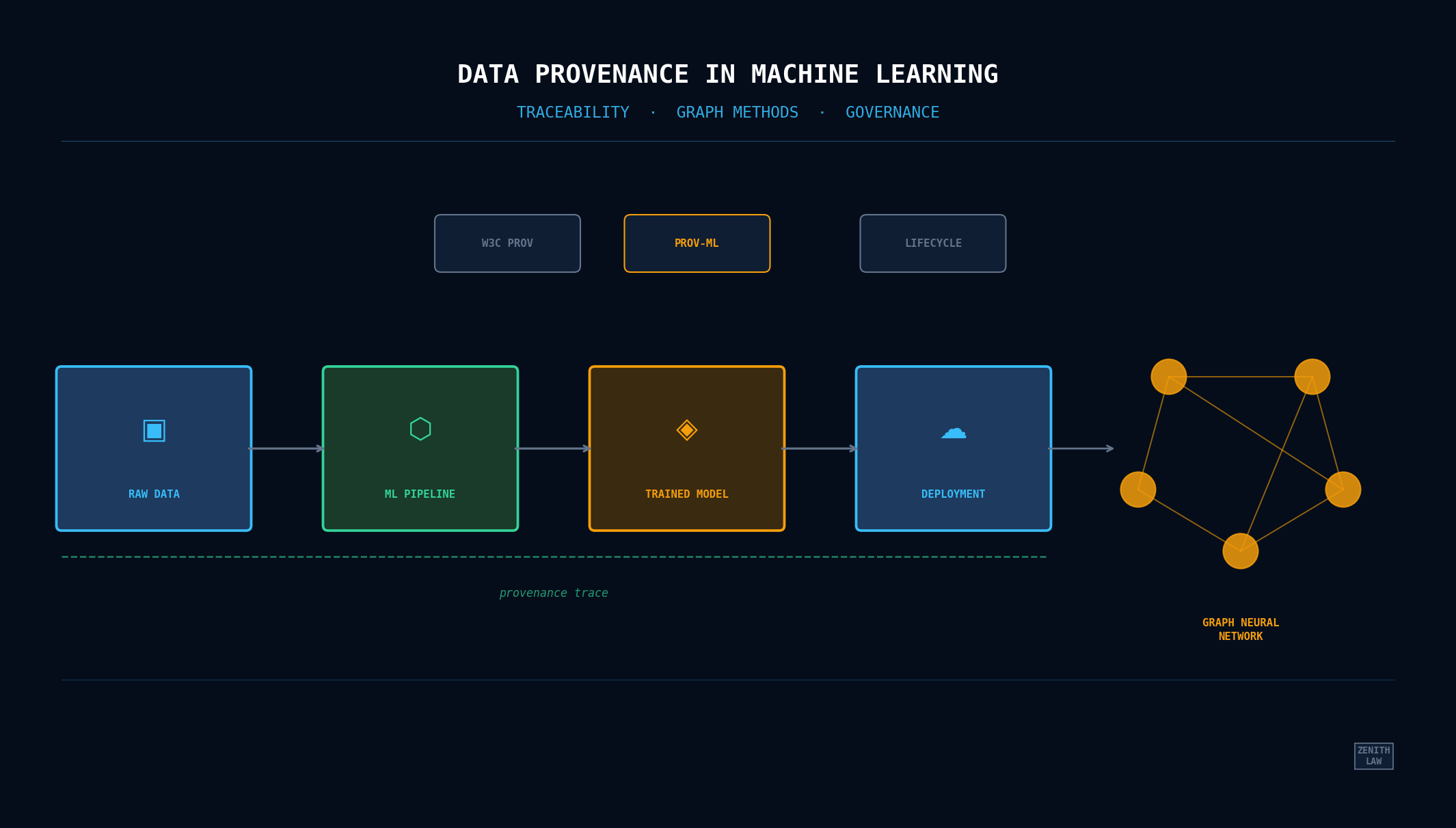
Data provenance in machine learning tracks where training data came from, how it was transformed, and which model versions resulted. Three scholarly papers evaluate this with graph neural networks, integration prototypes, and the PROV-ML standard....
Published 12 April 2026 by Zenith Law
This article synthesizes insights from nine educational videos and nine scholarly works on large language models. It traces the evolution from the 2017 Transformer paper through GPT-3, alignment research, knowledge distillation, federated learning...
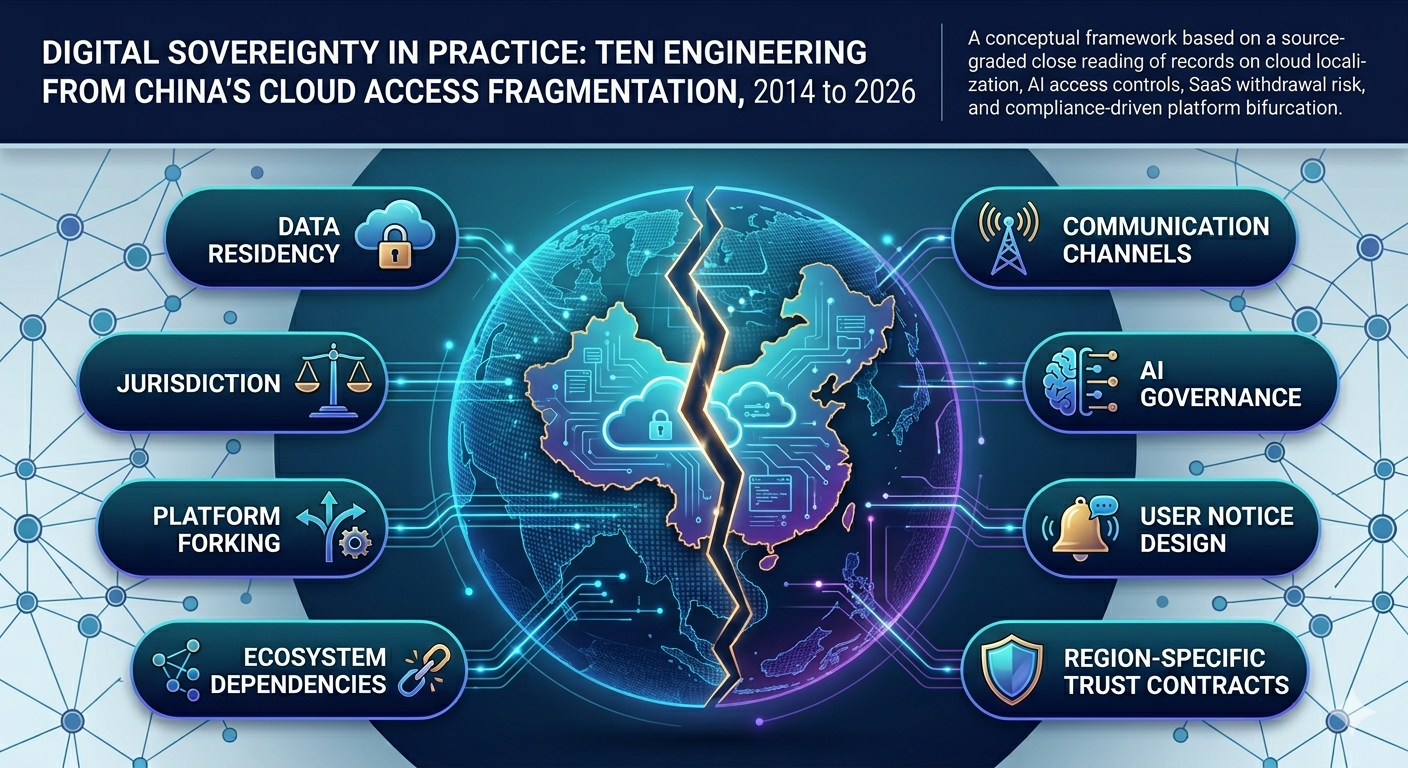
Published 10 April 2026 by Zenith Law
Cross-border SaaS delivery in China operates under a partitioned model driven by regulatory sovereignty, data localization law, and geopolitical risk. Azure, Salesforce, Unity, and AI services have all bifurcated or been blocked. This analysis rec...
Published 9 April 2026 by Zenith Law
On 30-31 March 2026, malicious axios npm versions 1.14.1 and 0.30.4 injected a counterfeit dependency that executed install-time malware across macOS, Windows, and Linux. Every material claim is mapped to verified sources. Evidence is separated fr...